All Blogs
How ZeroThreat Automates Web and API Security Testing Without Configuration

Blog Overview: This blog explains how ZeroThreat eliminates setup complexity and security expertise from application security. Learn how its AI-powered, autonomous pentesting platform enables continuous web and API protection without configuration, manual validation, or reliance on scarce AppSec specialists.
Automation is everywhere. And modern application security is supposed to be automated as well.
But in reality, most security teams are still spending weeks configuring scanners, tuning false positives, writing custom scripts, and manually validating findings, just to answer one question:
Is this vulnerability actually exploitable?
Traditional penetration testing tools or vulnerability scanners were built for static websites, predictable workflows, and slow-release cycles. On the other hand, today’s applications are dynamic SPAs, API-driven architectures, microservices, and constantly shipping CI/CD pipelines. Most security tools haven’t been kept up.
And the result we get is:
- Long setup cycles
- High false-positive rates
- Heavy reliance on security specialists
- Slow remediation validation
- Limited coverage of business logic abuse
And considering all the drawbacks and challenges faced by security teams, an AI-powered automated pentesting tool - ZeroThreat was built.
ZeroThreat is designed specifically to eliminate those friction points, not by simplifying scanning, but by redesigning how automated security testing works.
This article explains exactly how ZeroThreat removes setup complexity and reduces the need for specialized security expertise, while increasing testing depth, accuracy, and real-world risk validation.
Run AI-powered pentesting with zero configuration or complexity. Launch Your First Scan
On This Page
- Why AppSec Still Requires “Experts”
- How ZeroThreat Removes Complexity
- What “Zero Setup” Really Means
- Rethinking AppSec for Modern Applications
The Real Problem: Why AppSec Still Requires “Experts”
AppSec was supposed to become easier with automation. Instead, many experts invest more time managing tools than reducing risk and preventing vulnerabilities. The reason is structural: most security testing platforms still rely on static logic, rigid scanning rules, and manual configuration that assumes a stable, predictable application environment.
While talking about today’s web apps, they are dynamic, API-driven, multi-role, and continuously deployed systems. They rely heavily on client-side rendering, token-based authentication, microservices, and complex state transitions.
As we know, traditional tools were never designed for this level of architectural complexity. As a result, extracting meaningful results from them requires skilled security professionals who understand not only how attacks work, but how the scanner itself behaves.
Setup is Not Simple
In many organizations, “turning on” a DAST tool or traditional tool is just the beginning. Teams must configure authentication flows, handle CSRF tokens, manage session expiration, tune crawl behavior, define scope exclusions, and prevent destructive testing in production environments. If the application includes multiple user roles or dynamic UI logic, the configuration effort multiplies.
What’s often overlooked is that this setup is not a one-time task. Every UI change, API modification, authentication update, or workflow adjustment can break the scanner’s logic. Security engineers must constantly revisit configurations to maintain coverage. Over time, this becomes operational overhead disguised as automation.
Instead of accelerating security, traditional tools create a maintenance burden that only experienced practitioners can manage effectively.
Noise Forces Manual Validation
Even after you properly configure the tool, most legacy scanning tools generate a high volume of findings that require human triage. They flag potential injection points, misconfigurations, or anomalous responses, but they do not validate whether an attack truly succeeds.
This is where expertise becomes mandatory.
Security engineers must manually:
- Reproduce suspected vulnerabilities
- Confirm exploitability
- Determine if sensitive data is actually exposed
- Evaluate whether authorization boundaries can truly be bypassed
- Assess business impact beyond technical severity
Without this validation step, vulnerability reports become unreliable. With it, automation becomes partially manual again.
The problem isn’t that vulnerability scanners find nothing. The problem is that they find too much, without any context or evidence.
Modern Attack Paths are Multi-Step and Contextual
Real attackers rarely exploit isolated issues. They chain weaknesses together. A reflected input flaw may lead to token extraction. A minor authorization oversight may enable privilege escalation. An exposed internal API might allow data enumeration when combined with session abuse.
However, traditional tools struggle with this because they operate transactionally, with requests, payloads, and responses. They don’t reason across workflows or adapt their approach based on observed behavior. They lack contextual memory and decision-making capabilities.
As a result, identifying real-world exploit chains requires human pentesters who can think adversarially. That dependency on human reasoning is exactly what prevents AppSec from scaling.
Business Logic is Still Largely Manual Territory
When we talk about business logic abuse, perhaps it’s the most significant blind spot in automated security testing. Through static payload testing, you can detect fraud scenarios, order manipulation, state transition bypasses, pricing logic exploitation, and workflow abuse.
Detecting these issues requires understanding:
- Application intent
- User role interactions
- State progression
- Transaction dependencies
- Edge-case workflow behavior
Expertise Becomes the Bottleneck
We all know, there’s a huge gap in finding security talent. Senior AppSec engineers and skilled pentesters are expensive and difficult to scale across hundreds of applications. When security tooling requires constant tuning, manual validation, and interpretation, it amplifies the talent shortage.
This leads to a bottleneck:
- Development moves fast.
- Applications grow more complex.
- Attack surfaces expand.
- Security tools require specialists.
The result is uneven coverage, delayed remediation, and growing risk exposure between releases.
Automation was meant to remove this bottleneck. In practice, it has often shifted the burden rather than eliminated it.
How ZeroThreat Removes Complexity
Traditional application security tools demand configuration, rule tuning, scripting, and deep expertise before delivering value. ZeroThreat removes these operational barriers by embedding security intelligence directly into the platform.
In fact, ZeroThreat follows best practices to secure web applications as an attacker-simulation problem, not as a payload injection problem.
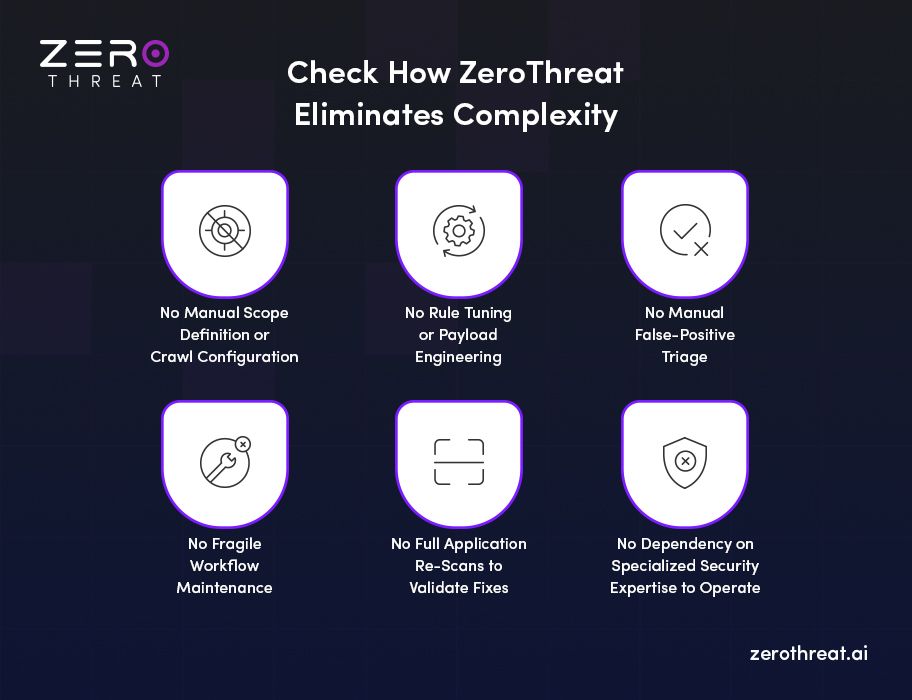
1. No Manual Scope Definition or Crawl Configuration
Most DAST tools and other pentesting tools require teams to define scan scope, configure crawl depth, handle session management, and script authentication flows. This setup process often consumes more time than actual testing.
ZeroThreat’s pentesting tool eliminates this entirely.
It understands how modern applications manage tokens, sessions, and role transitions without requiring engineers to script those flows manually. Authenticated testing begins immediately, without custom scripting layers that break every time the application updates.
Therefore, security teams no longer spend cycles maintaining brittle login automation. ZeroThreat’s AI engine adapts to the application instead of forcing the application to adapt to the security testing tool.
There is no need for custom crawl scripts or pre-scan configuration. The system intelligently discovers the attack surface before testing it.
Continuously discover and validate real vulnerabilities without manual effort. Activate Continuous Testing
2. No Rule Tuning or Payload Engineering
Legacy security testing platforms depend heavily on predefined crawling logic. Security teams must define URL patterns, exclude dynamic routes, manage parameter handling, and manually adjust scope rules to ensure coverage without disruption.
In fact, modern applications make this even harder. SPAs render content dynamically. APIs expose hidden endpoints. Client-side routing bypasses traditional crawling logic.
Here, ZeroThreat removes this configuration step entirely. It maps dynamic routes, APIs, forms, and state transitions automatically as it interacts with the application in real time. Instead of relying on static crawl rules, it explores application behavior the way a real attacker would, by observing responses and adapting navigation paths dynamically.
There is no crawl file to maintain. No fragile scope configuration to update when a new feature is released.
Here, the coverage of assets evolves with the application.
3. No Manual False-Positive Triage
Traditional scanners often generate significant noise because they rely on pattern matching instead of exploiting validation. Security engineers must manually suppress false positives, tune payload sensitivity, and repeatedly validate findings before reporting them internally.
ZeroThreat eliminates this manual tuning process by validating exploitability during testing. It does not simply detect suspicious responses, it attempts to confirm whether an attack path truly succeeds and whether sensitive data can be accessed.
Since findings are evidence-backed and exploit-validated, there is no need for extensive rule suppression or post-scan cleanup. The system reduces noise at the source rather than asking engineers to filter it afterward.
This dramatically reduces time spent triaging and increases confidence in reported issues.
4. No Fragile Workflow Maintenance
Every day, some new features are integrated into applications. There could be modified flows, updated UI logic, and changing APIs as well. Traditional scanner configurations often break silently when these updates occur. Security teams may not realize coverage gaps exist until much later.
ZeroThreat removes this fragility by using adaptive, browser-level interaction to navigate applications the way real users do. It executes dynamic workflows, handles client-side rendering, and maintains state without relying on rigid, pre-recorded sequences.
When the application changes, the platform adjusts its navigation strategy automatically. There is no dependency on brittle automation scripts that require ongoing manual repair.
This makes continuous security testing sustainable.
5. No Full Application Re-Scans to Validate Fixes
In many environments, validating a remediation requires re-running a complete scan of the entire application. This consumes time and operational overhead, which slows down development cycles and frustrates both security and engineering teams.
However, ZeroThreat allows you to retest issues individually instantly without reconfiguring the scope or restarting full-scan workflows. Exploit paths can be revalidated in isolation, dramatically accelerating remediation confirmation.
This eliminates repetitive operational work and ensures security validation keeps pace with modern CI/CD pipelines.
6. No Dependency on Specialized Security Expertise to Operate
This is one of the most important shifts.
ZeroThreat does not require deep scanner expertise to produce meaningful results.
While leveraging traditional tools, security engineers would have to configure, interpret, and validate output. ZeroThreat is designed so that validated findings, exploit evidence, and contextual impact are surfaced automatically.
AppSec engineers can focus on architecture and threat modeling rather than maintaining scanning infrastructure. Security leaders gain reliable visibility without needing large teams dedicated solely to tool management.
The platform removes operational dependency, not by reducing depth, but by automating the reasoning that previously required specialists.
What “Zero Setup” Really Means
When we talk about “Zero setup” in application security, it does not mean shallow scanning or limited coverage. It means removing the operational engineering burden that traditionally sits between a security team and meaningful risk visibility.
While choosing ZeroThreat as your agentless web and api security scanning platform, you don’t have to write any custom scripts, scan logic around UI workflows, and deploy agents inside the apps.
The platform adapts to how the application behaves in real time, maintains session context, explores dynamic routes, and validates exploit paths without requiring ongoing human tuning.
For Security Leaders: It means faster time to coverage and reduced operational overhead. There is no extended implementation cycle, no heavy dependency on senior specialists to configure and maintain the tool, and no recurring cost of reworking scans after every product release.
For AppSec Engineers: It means spending time on high-value security strategy instead of scanner maintenance. This helps teams to focus on strengthening architecture, reviewing complex edge cases, and reducing true business risk.
In fact, zero setup, ultimately, is not about convenience. It is about removing friction that prevents security from scaling alongside modern development.
Flexible plans for startups, SaaS, and enterprise environments. See Pricing Plans
Rethinking AppSec for Modern Applications
Application security doesn’t have to be defined by complex setup, manual tuning, and constant expert oversight. As modern apps grow more dynamic and release cycles accelerate, security must become adaptive, autonomous, and scalable.
ZeroThreat represents that shift. It eliminates configuration overhead while delivering validated, real-world exploit visibility. Instead of managing tools, teams can focus on reducing actual risk.
Ready to experience security without the setup burden? Sign up now and start scanning without any configuration.
Frequently Asked Questions
How is ZeroThreat different from traditional DAST tools?
Traditional DAST tools detect patterns. ZeroThreat validates real exploit paths. It uses agentic AI to simulate attacker behavior, reduce false positives, and eliminate manual validation cycles.
Does ZeroThreat require agents or code changes?
Can ZeroThreat test modern SPAs and APIs?
How does ZeroThreat enable automated web and API security scanning without agents or configuration?
Can ZeroThreat be used by teams without dedicated AppSec or security engineers?
Why is zero-setup security scanning critical for fast-moving DevOps and SaaS teams?
How does ZeroThreat ensure security scans remain effective without manual rule tuning?
Why are organizations moving away from tool-heavy AppSec stacks toward zero-setup platforms?
What operational challenges do teams face when security scanning depends on manual configuration?
Explore ZeroThreat
Automate security testing, save time, and avoid the pitfalls of manual work with ZeroThreat.


