98.9%
AI-Enhanced Accuracy

90%
Reduced Manual Pentest

ZERO
Configuration Required

10X
Faster Scan Result
AI-Powered Attack Simulation Across Application Surfaces
ZeroThreat uses a unified AI attack simulation engine to test applications in context, automatically selecting attack paths, validating exploitability, and confirming real risk.
High-Level Architecture for AI-Driven Pentesting
ZeroThreat’s architecture is designed to support continuous, automated pentesting across web applications and APIs by supplying targeted attack payloads for each identified request. The platform continuously runs relevant attack techniques based on observed application context, exposed surfaces, and real-world attacker methods.
AI-driven pentesting acts as the execution engine, coordinating discovery and exploit validation while evaluating findings in context. By simulating 130K+ real-world attack paths, ZeroThreat scales testing without relying on static rules or isolated checks, ensuring results reflect actual exploitability.
- Context-Aware Discovery
- Intelligent Payload Generation
- Exploitation and Verification Using Multimodal AI
- Risk-Based Prioritization
- AI-Powered Remediation Reports
How ZeroThreat Identifies Real Risk
ZeroThreat’s automated pentesting follows a structured scan flow to assess application security from onboarding through validated reporting.
Target Intake
A web application or API endpoint is added with the required access level, authentication context and scope.
Discovery & Mapping
The platform identifies reachable attack surfaces, application workflows, and exposed endpoints.
Security Testing & Simulation
Automated testing simulates advanced attack behaviors across the discovered paths.
Validation & Risk Analysis
Identified issues are validated and analyzed to assess exploitability, severity, and potential impact.
Reporting & Re-Testing
Findings are documented with remediation guidance, and re-scans can be performed to confirm fixes.
Data Handling & Privacy Controls
ZeroThreat is designed to process only the data required to perform application security testing, with controls in place to limit exposure and retain customer ownership.
Purpose-Limited Processing
Only data necessary for discovery, testing, and validation is processed during scans.
Customer Data Isolation
Each customer’s scan data is logically isolated to prevent cross-access between environments.
Regional Data Storage Controls
Support for region-specific scan execution and data storage is available to align with regulatory and residency requirements.
Customer Ownership
All scan results and findings remain the property of the customer. The data is used only for security testing and reporting.
Secure Data Transmission & Encryption
All data transmitted during scanning and reporting is encrypted in transit and at rest using industry-standard protocols to protect confidentiality and integrity.
Cost-Effective Privacy Controls
We provide enterprise-grade data isolation, retention, and regional controls as part of the platform, without increasing operational costs.
AI Decision & Analysis Layers
ZeroThreat uses AI to assist with analysis and decision-making during web app and API security testing. It identifies complex app behavior and security findings.
Context Understanding
AI helps understand application state, request sequences, and access conditions to understand how different components interact during testing.
Noise Reduction
Findings are analyzed to distinguish between theoretical issues and conditions that are more likely to represent real security risk.
Risk-based Prioritization
Identified issues are evaluated and ordered based on exploitability and potential impact, rather than volume or raw severity alone.
Support for Complex Attack Paths
AI assists in analyzing multi-step behaviors and chained conditions that may contribute to higher-risk security scenarios.
Adaptive Testing Logic
AI dynamically adjusts testing strategies based on application responses, behavior changes, and discovered attack surfaces to improve coverage.
Exploit Validation Support
AI assists in validating whether identified weaknesses can be practically leveraged, helping reduce false positives.
Safety & Testing Controls
ZeroThreat is designed to operate safely against live applications, with controls in place to minimize risk and reduce disruption on production applications.
Non-Intrusive Scanning Approach
Scanning techniques are designed to avoid destructive actions and focus on validating security behavior without altering application state.
Rate Limiting and Execution Safeguards
Scan activity is regulated through built-in limits and safeguards to prevent excessive load or unintended behavior.
Testing Environment Isolation
Each customer’s testing environment and scan execution are isolated to prevent cross-tenant interaction or impact.
Production-safe controls
Testing is conducted with controls in place to minimize disruption across development, staging, and production environments.
Explore Real-World Security Impact

5.0

"ZeroThreat gives our team an easy, highly accurate way to test the security of our applications and APIs. Its AI-powered engine for automation is both powerful and straightforward to use."

Frequently Asked Questions
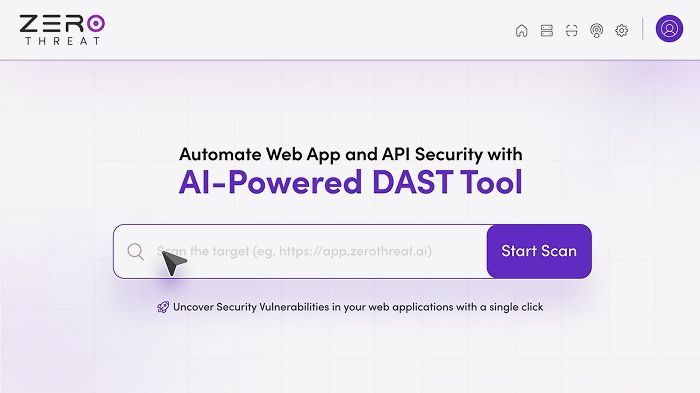
Does ZeroThreat require agents, integrations, or complex setup?
No. ZeroThreat operates without agents or intrusive configurations. You can initiate security testing quickly without modifying your application architecture or deployment pipelines.
Is it safe to run ZeroThreat on production environments?
How does ZeroThreat reduce false positives?
Who is ZeroThreat built for?
What types of applications can ZeroThreat test?
How does ZeroThreat prioritize security findings?
Can ZeroThreat handle complex, multi-step attack paths?
How does ZeroThreat protect customer data during scans?
Spend Less Time Validating. More Time Fixing.
AI-powered exploit validation cuts false positives and accelerates remediation, saving hours every sprint.