
All Blogs
What is Agentic Pentesting? Agent-Powered Autonomous Security Testing
Quick Overview: Gain a deep understanding of agentic pentesting and how it’s replacing traditional manual audits with autonomous, human-like reasoning. This guide explores multi-agent architectures, five-phase security cycles, and real-world use cases for API and web application security. Discover how to eliminate false positives through exploit validation while scaling your security at machine speed.
In 2026, the pace of digital innovation has officially outrun the speed of human security. With a new vulnerability discovered every 17 minutes, security teams are facing a structural backlog that manual testing simply cannot clear. While traditional scanners struggle with a high false positive rate, and manual pentests remain too slow to scale, a new edge has emerged: Agentic Pentesting.
Agentic pentesting is a fundamental shift toward autonomous security agents that scan and validate exploits exactly like a human attacker. By leveraging multi-agent architectures, these systems can reduce incident response times by up to 96% and lower the cost of a data breach by an average of $2.22 million.
In this guide, we’ll dive into how agentic pentesting is redefining AppSec and why it’s becoming the core of modern CI/CD pipelines. Plus, we’ll learn how you can choose the right tool to leverage agentic penetration testing for securing your web apps and APIs.
Experience autonomous agentic penetration testing built for modern attack surfaces Sign Up Free
On This Page
- What is Agentic Pentesting?
- Agentic Pentesting vs Traditional Pentesting
- How Agentic Penetration Testing Works
- Working of Multi-Agent Architecture for Pentesting
- Key Benefits of Agentic Penetration Testing
- Limitations and Considerations of Agentic Pentesting
- What to Look for in an Agentic Pentesting Platform
- Real-World Use Cases of Agentic Penetration Testing
- Final Thoughts
What is Agentic Pentesting?
Agentic pentesting is an AI agent-based approach to penetration testing where autonomous security agents actively discover, exploit, and validate real security risks. It goes beyond scanning by behaving like an intelligent attacker that can plan, adapt, and verify impact on its own.
Unlike traditional or rule-based automated pentesting, agentic penetration testing uses AI agents for security testing that work together. Each agent has a clear role. One focuses on reconnaissance and attack surface discovery. Another handles exploitation. Others validate whether a vulnerability is truly exploitable or just a false positive. This multi-agent architecture allows you to perform more accurate testing.
What makes agentic pentesting different is how they find the vulnerability. These agents do not just follow static templates. They observe responses, adjust attack paths, and perform agent assisted exploits to find actual vulnerabilities. It helps reduce false positives and highlights issues that actually matter.
Agentic penetration testing also supports continuous pentesting. It can run across development cycles, APIs, and web applications. This makes it suitable for modern CI/CD pipelines where security needs to move fast.
In simple words, agentic testing combines automation, intelligence, and validation. The result is a clearer risk context, faster insights, and security teams that can focus on fixing what is truly exploitable.
Agentic Pentesting vs Traditional Pentesting
Agentic pentesting and traditional pentesting follow very different approaches to security testing. One relies on autonomous AI agents and continuous execution, while the other depends on manual expertise and time-bound assessments. Here is how they differ:
| Aspect | Agentic Pentesting | Traditional Pentesting (Human-Led) |
|---|---|---|
| Testing Approach | Uses multiple AI agents that autonomously discover, exploit, and validate vulnerabilities. | Relies on skilled human testers performing manual assessments. |
| Speed & Cadence | Fast and continuous. Can run on demand or integrated into CI/CD. | Slower, periodic tests (often annual or quarterly). |
| Coverage | Broad. Can test many endpoints, APIs, and attack vectors continuously. | Limited to scoped engagements with fixed time windows. |
| Cost | Lower over time. Automation reduces manual effort and expensive consultancy fees. | Higher. Skilled experts and long testing periods increase costs. |
| Context Awareness | Good at technical exploit paths and attack surface discovery. May struggle with deep business logic. | Strong contextual insight into logic flaws, workflows, and custom exploit paths. |
| Exploit Validation | Agents validate exploitability systematically and often reduce false positives. | Humans validate impact and provide tailored remediation guidance. |
| Scalability | High. Can test multiple systems and environments at once. | Limited. Human bandwidth restricts scale. |
| Continuous Testing | Designed for ongoing checks, fitting DevSecOps and continuous security. | Usually single engagement with a snapshot in time. |
| Role in CI/CD | Easily integrated for shift-left security and frequent feedback loops. | Harder to integrate due to scheduling and manual effort. |
| Best Use | Frequent vulnerability discovery, automated exploit chaining, broad attack surface coverage. | Deep context-aware testing, complex business logic, creative attack paths. |
How Agentic Penetration Testing Works: Five-Phase Cycle
To understand how agentic pentesting actually works, you have to look past the simple "scan and report" model. Instead of a linear script, this process functions as a continuous, intelligent loop.
Here is a breakdown of the five-phase cycle that specialized AI agents follow to detect security vulnerabilities.
1. Discovery
The first step is mapping your entire attack surface. Unlike older tools that need a list of URLs to start, autonomous agents act like digital explorers. They find shadow APIs, undocumented APIs, and complex data handling processes that often go unnoticed. By adapting their reconnaissance based on what they find, they ensure nothing is left undiscovered.
2. Scanning
Once the map is ready, the agents begin their analysis. This isn't just about running a list of known bugs. The agents actually analyze application responses and detect flaws in business logic. For example, if an agent is testing a checkout flow, it reasons how payments and sessions are managed, rather than just throwing generic injection patterns at a text box.
3. Exploitation
This is where agentic penetration testing truly separates itself from traditional tools. Instead of just flagging a "potential" vulnerability, the agents attempt to prove it.
- Multi-step Chains: Agents chain together different exploits to see how deep they can go.
- Real Validation: They demonstrate working exploits in safe, sandboxed environments.
- Business Impact: By proving exploitability, they show you the actual risk to your business rather than a theoretical threat.
4. Reporting
Once issues are confirmed, detailed reporting begins. Good reports go beyond a list of bugs. They explain the attack chain, show reproduction steps, and rank issues by business risk, not just severity scores. Each report includes:
- Full Attack Chains: A clear map of how the agent got in.
- Reproduction Steps: Exact data that developers can use to see the bug for themselves.
- Risk Prioritization: Findings are ranked by their real-world impact and business risk, not just a standard severity score.
5. Remediation
The cycle doesn’t end with a "broken" sign; it ends with a fix. AI-powered remediation provides specific code snippets and architectural advice tailored to your environment. Most importantly, once you apply a patch, the agents can automatically re-test the area to confirm the vulnerability is truly gone.
This five-phase cycle completes the security loop. Most tools stop at scanning or exploitation. Agentic penetration testing goes further by providing actionable insight and real proof of issues. It helps teams fix problems faster with even more reliability.
See how ZeroThreat’s autonomous agents detect security flaws in web apps and APIs Explore Agentic Testing
The Multi-Agent Architecture for Pentesting: How it Works
Building an effective system for agentic penetration testing is far more complex than simply pointing an LLM at an application and hoping for the best. In fact, early research shows that unmanaged AI can often "hallucinate" vulnerabilities by faking the exploitation process itself.
To avoid these pitfalls, a successful architecture relies on specialization, strict rules, and intelligent management. This is typically achieved through a three-layer multi-agent architecture that mirrors the collaborative nature of a human red team.
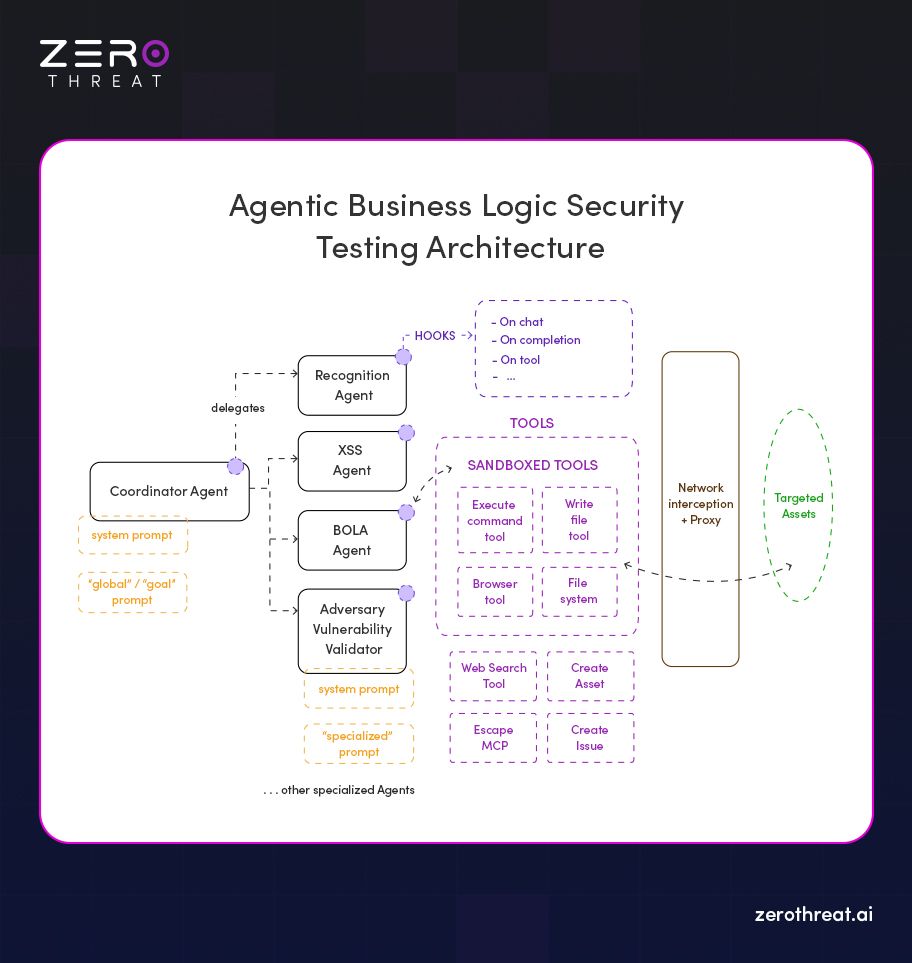
1. The Coordinator Agent
The coordinator isn’t a scanner or tester. It’s the planner. It sets the testing goals. It breaks down the pentest into tasks. Then it assigns those tasks to specialists. It also keeps an eye on every agent so nothing goes off track. The coordinator’s job is not to test itself, it is to manage the team (agents). This ensures the system stays safe, orderly, and predictable in how it tests your applications.
2. The Specialized Agents
Instead of one general AI trying to do everything, this layer consists of "Expert Agents" that focus on a single attack vector or phase of the lifecycle. Typical roles include:
- Recognition Agent: This agent is responsible for mapping routes, analyzing the application's unique architecture, and finding entry points.
- BOLA Agent: A specialist that specifically hunts for Broken Object Level Authorization and privilege escalation flaws.
- XSS Agent: Focuses on cross-site scripting by using context-aware payloads rather than generic scripts.
- Adversarial Vulnerability Validator: This critical agent confirms that exploits actually work in real-world conditions, preventing false positives.
These agents don’t guess or hallucinate. They operate within defined boundaries and share results through an intelligence layer. This separation lets the system cover more ground without overwhelming any single model. It also improves accuracy and reduces noise.
3. The Sandboxed Tools
For safety and precision, agents do not interact directly with your live application in an unmonitored way. Instead, they use a suite of sandboxed tools built with deterministic programming languages that act like secure testing environments.
Sandboxed tools can:
- Send controlled web requests.
- Execute browser automation safely.
- Intercept network traffic.
- Create controlled test assets.
This safety layer prevents agents from causing unintended damage or misinterpreting their actions. It keeps testing deep, thorough, and secure.
Key Benefits of Agentic Penetration Testing
Agentic pentesting provides a massive advantage by moving beyond the limits of manual work. It allows your security team to stop choosing between speed and depth. By using autonomous agents, you gain a continuous, expert-level defense that scales effortlessly alongside your growing application.
Unmatched Coverage
Traditional testing often forces you to pick only your most critical apps due to budget or time constraints. Agentic systems remove these limits, providing 100% coverage across all your APIs and endpoints. They can even uncover hidden assets and complex business logic flaws that standard tools usually miss.
Cost-Effective
Manual pentests are expensive and hard to scale because they rely entirely on human effort and expertise. Switching to an agentic model significantly lowers labor costs while improving your overall ROI. You can double your testing frequency without needing to hire a team of specialized security experts.
High Speed
While a manual pentest can take weeks to return a final report, agentic AI operates at machine speed. You can complete a deep, comprehensive vulnerability assessment in just a few hours. This real-time feedback allows your developers to find and fix vulnerabilities as they happen.
Better Accuracy
The biggest problem with older automated scanners is the "noise" created by endless false positives. Agentic pentesting solves this by validating every finding through proof-of-exploitability before alerting you. This high-signal reporting means your team only spends time on real, proven risks.
Simplified Compliance
Meeting standards like PCI DSS, GDPR, or SOC 2 can be a manual reporting nightmare. Agentic platforms simplify this by automatically mapping findings to major regulatory frameworks. You can generate audit-ready reports on demand, providing clear evidence of your continuous security posture whenever it's needed.
Limitations and Practical Considerations of Agentic Pentesting
While agentic penetration testing is a massive leap forward, it’s not a magic fix for every security challenge. Like any emerging technology, it has boundaries that teams need to navigate carefully to get the best results.
One of the biggest hurdles is the risk of "AI hallucinations". Without strict rules, early-generation agents can sometimes fake an exploitation process that didn't actually happen.
Current Practical Challenges Are...
- The Creativity Gap: AI is incredibly fast, but it can still struggle with the "out-of-the-box" intuition a human hacker uses for unique, multi-step business logic attacks.
- Custom Environments: Highly non-standard authentication flows or niche, proprietary protocols can sometimes confuse autonomous agents.
- Contextual Blindness: Agents might miss complex chains that require understanding "out-of-scope" business context that isn't explicitly defined in the code.
Understanding these gaps doesn't make agentic testing less valuable; it just means you should use it to amplify, not entirely replace, human expertise. By setting realistic expectations and selecting a pentesting platform with strong safety layers, you can focus on the high-signal risks that matter most.
Choose from ZeroThreat’s pricing plan designed for continuous agentic pentesting View Pricing
What to Look for in an Agentic Pentesting Platform
Choosing the right agentic pentesting platform is about finding a tool that thinks like a hacker but works like a software engineer. Look for platforms that prioritize safety, clarity, and practical integration to get real value.
Clear and Accurate Vulnerability Validation
A good platform doesn’t just flag weaknesses. It confirms whether they are exploitable and shows proof. This helps reduce noise and false positives that waste time. Validation should include clear evidence, like reproduction steps or attack paths.
Specialized and Context-Aware Agents
Look for platforms that use specialized agents trained for specific tasks — like reconnaissance, scanning, exploit chaining, and validation. Agents should adapt based on findings and context. This improves real coverage across APIs, web apps, and logic flows.
Safe Execution and Sandboxing
Testing must never break systems or affect production. Leading platforms provide sandboxed execution for agents so they run safely. You should be able to control what gets tested and how.
Integration with Workflows and CI/CD
Security teams need continuous feedback. The platform should integrate with CI/CD pipelines and development workflows. This helps catch issues early and often. It should trigger tests on new releases or changes.
Actionable Reporting and Remediation Guidance
Reports should be clear, risk-based, and easy to act on. They should map findings to impact, show evidence, and provide remediation steps. This is essential for developers and auditors alike.
Choosing a platform with these qualities will help you get deeper insights, better accuracy, and actionable results from your agentic pentesting efforts.
Real-World Use Cases of Agentic Penetration Testing
Agentic pentesting brings real value where traditional methods struggle. It adds depth, speed, and continuous coverage to security testing. This makes it useful across modern development and risk management workflows. Teams adopting agentic penetration testing are able to find real attack paths and secure systems with less effort.
Continuous Security Validation
Modern applications change fast. Every code push can introduce new risks. Agentic pentesting fits into CI/CD pipelines and tests on every release. This gives teams constant visibility into their security posture instead of waiting for annual or quarterly tests.
API and Modern Web App Testing
APIs and single-page applications have complex logic flows. Traditional tools often miss logic flaws or chained attacks. On the other hand, agentic systems simulate real threat tactics across these areas to catch deeper issues.
Pre-Compliance Preparation
Before audits like GDPR, PCI DSS, SOC 2, or ISO 27001, teams need thorough testing. With agentic penetration testing, organizations can identify and fix vulnerabilities early, making formal compliance checks easy and effortless.
Large Attack Surface Exploration
Enterprises often have many systems, endpoints, and microservices. This advanced penetration testing scales to test broad environments without exhausting manual resources. It finds gaps that might slip through in manual assessments.
Risk Prioritization and Evidence-Backed Results
Modern security teams don’t just want lists of issues; they want context. Agentic pentesting tools validate actual exploitability and links findings to real impact. This reduces noise and helps teams act strategically.
Agentic pentesting blends autonomous testing with real-world attack simulation. It supports continuous delivery, deep logic checks, and better risk understanding across complex environments.
Ready to integrate autonomous pentesting into your CI/CD pipeline? Speak With an Expert
Final Thoughts
Agentic pentesting changes how security testing is done. Instead of one-time scans or manual efforts, it uses autonomous agents to continuously discover, test, exploit, and validate security issues across applications and APIs. This approach helps teams detect real-world risks earlier, reduce blind spots, and keep security aligned with fast-moving development cycles.
As we have explored, the shift to an agentic approach brings several key advantages to your security lifecycle:
- Autonomous Validation: Unlike traditional tools that flag "potential" issues, agents prove real-world risk by safely exploiting vulnerabilities in sandboxed environments.
- Deep Business Logic Testing: Specialized AI agents understand complex workflows, allowing them to find sophisticated flaws like BOLA that standard scanners typically miss.
- Continuous CI/CD Integration: Agentic systems operate seamlessly within your pipelines, providing 100% asset coverage and real-time results every time you ship new code.
- Reduced Manual Effort: By automating the most time-consuming parts of a pentest, teams can save up to 90% of their testing time and significantly lower labor costs.
Agentic pentesting is like a security team testing your project continuously and alerting you with remediation steps. If you are looking to leverage the power of agentic penetration testing for your web apps and APIs,try using ZeroThreat. It focuses on proven exploitability and autonomous reasoning, providing the clarity you need to fix security vulnerabilities that matter most.
Frequently Asked Questions
What is agentic pentesting?
Agentic pentesting is an AI agent-driven approach where autonomous security agents actively discover, exploit, and validate real vulnerabilities. It goes beyond scanning by adapting to application behavior and confirming actual risk. The goal is clearer findings with near-zero false positives.
How does autonomous pentesting work?
Can AI replace manual penetration testing?
Why use agentic pentesting instead of automated scanners?
What are the advantages of agentic pentesting?
Is agentic pentesting scalable for large environments?
Do autonomous pentesting agents generate false positives?
How do autonomous pentesters validate vulnerabilities?
How to choose an AI pentesting platform?
Explore ZeroThreat
Automate security testing, save time, and avoid the pitfalls of manual work with ZeroThreat.


