All Blogs
How Regional Data Scanning and Storage Control Helps Meet Security Compliance

Quick Overview: Data residency and sovereignty are now critical for teams operating under GDPR, PCI DSS, and other data sovereignty frameworks. This guide covers what it means, why scan data residency matters legally and operationally, which industries face the strictest requirements, and how platforms like ZeroThreat give security teams direct control over where penetration test scans run and where findings are stored.
Data is no longer just a security concern; it’s a compliance liability. The global average cost of a data breach has reached $4.44 million, with regulatory fines and cross-border data exposure driving much of that impact.
At the same time, regulators are tightening control over where data is processed and stored. In 2025 alone, GDPR enforcement crossed €1.2 billion in fines, showing that data location is now a legal priority, not just a technical one.
This is where regional data scanning and storage control becomes critical. It gives organizations clear control over where scan data is processed and stored, helping them meet data residency requirements, reduce cross-border risks, and align with security compliance regionally and globally.
Deploy agentless, attacker-style testing that keeps your sensitive findings strictly local. Try for FREE
ON THIS PAGE
- What is Regional Data Scanning and Storage Control?
- Data Residency vs Data Sovereignty: What You Need to Know
- Benefits of Regional Data Scanning & Storage Control
- Regulatory Landscape Driving Data Residency Requirements
- Industry-Specific Data Sovereignty Compliance Requirements
- Challenges of Managing Data Residency in Cloud Security
- How ZeroThreat Enables Regional Data Scanning and Storage Control
- Conclusion: Taking Control of Data Scan and Storage Locations
What is Regional Data Scanning and Storage Control?
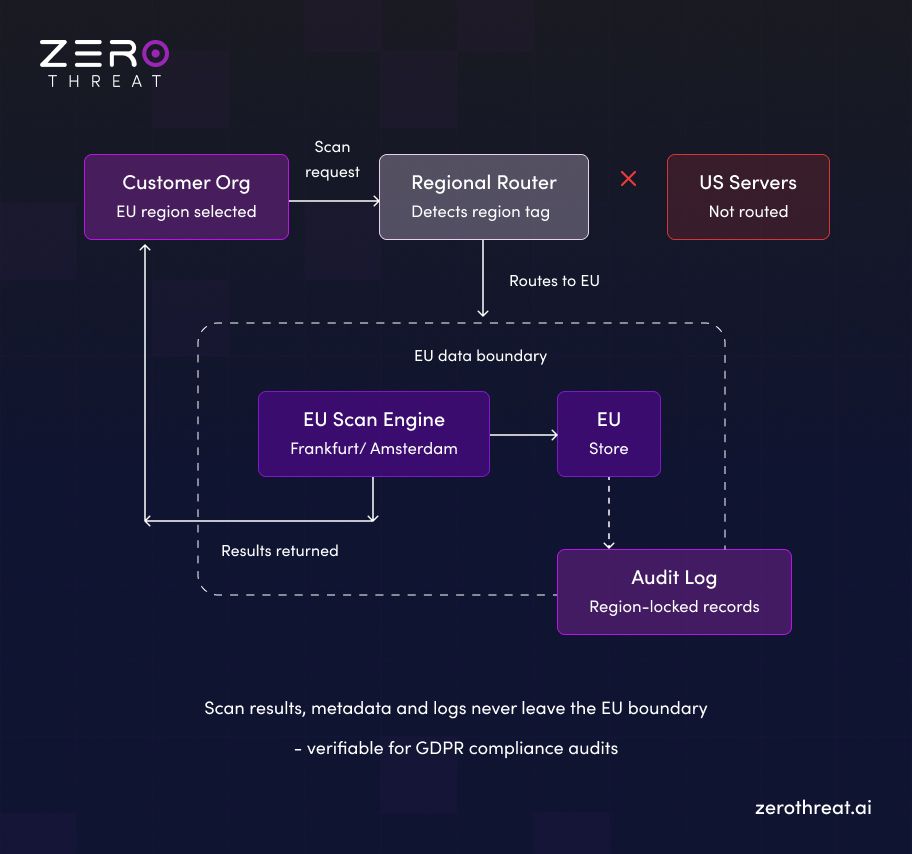
Regional data scanning and storage control is a specialized security configuration that allows organizations to define the exact geographic location where their application security testing occurs. It ensures that both the active scanning process and the resulting vulnerability data remain within a specific region’s borders.
This control is a critical pillar for maintaining data residency, which refers to the physical location of data. By localized scanning, businesses ensure that sensitive information such as PII discovered during a penetration test never leaves its home jurisdiction, satisfying strict legal requirements and internal governance policies.
From a compliance standpoint, this feature helps companies navigate complex laws like GDPR, HIPAA, or India’s DPDP Act. It bridges the gap between high-depth security testing and legal sovereignty, allowing global enterprises to run advanced API pentests while keeping their data footprint strictly regional and secure.
Here is an example of how regional data scan and storage control works:
Data Residency vs Data Sovereignty: What You Need to Know
To protect your organization, you need to know exactly where your data lives and who has authority over it. While these terms are often used interchangeably, they serve different roles in your security and compliance strategy.
| Aspect | Data Residency | Data Sovereignty |
|---|---|---|
| Definition | Refers to where data is physically stored | Refers to which country’s laws govern the data |
| Focus | Location of data | Legal control over data |
| Key Concern | Keeping data within a specific region | Ensuring data follows local regulations |
| Impact on Security | Limits where data can be stored | Defines how data must be handled and accessed |
| Cloud Relevance | Choosing a specific cloud storage region | Understanding legal obligations across regions |
To say it in one line: Data residency is about where your data lives, while data sovereignty is about who has authority over it.
Benefits of Regional Data Scanning & Storage Control
Selecting specific regions for security scans and storage empowers teams to protect sensitive findings while meeting legal mandates. This strategic control builds a foundation of trust and operational transparency.
- Strict Regulatory Compliance: Laws like GDPR and HIPAA often require data to stay within specific borders. Using regional controls ensures your security findings remain within these legal boundaries. This simplifies audits and keeps your organization aligned with strict global mandates.
- Enhanced Data Trust and Sovereignty: Choosing your scan and storage locations gives you direct authority over your digital assets. This prevents foreign jurisdictional oversight and ensures your sensitive security insights are managed under your own legal framework, significantly raising security trust.
- Improved Latency and Efficiency: Scanning data closer to your applications reduces latency and speeds up testing. Localized processing makes security checks faster for developers. This is especially helpful for teams running continuous security tests within their modern CI/CD pipelines.
- Operational Autonomy and Risk Mitigation: Regional controls help you stay independent from foreign state or corporate actors. Keeping your security findings in a sovereign environment mitigates risks like data exfiltration. It ensures that your security operations do not introduce unnecessary trust assumptions.
Stop guessing where your data goes. Run localized pentests with 98.9% accuracy. Pentest Securely
Regulatory Landscape Driving Data Residency Requirements
Understanding the global regulatory landscape is essential for any modern enterprise. Many countries now view data as a national asset, leading to laws that mandate where sensitive information can be processed and stored.
Here is a simplified breakdown of the key regulations currently driving data residency requirements across the globe:
| Regulation / Framework | Jurisdiction | Key Data Residency Requirement |
|---|---|---|
| GDPR | European Union | Personal data cannot be transferred outside the EEA without adequate legal protections in place |
| Schrems II (CJEU Ruling) | EU / Global | Invalidated EU-US Privacy Shield; organizations must now conduct Transfer Impact Assessments for US-bound data |
| BDSG | Germany | Supplements GDPR with stricter national rules; heightened controls apply to health and employment data |
| DORA | European Union | Financial entities must document and control ICT data processing locations as part of operational resilience |
| NIS2 Directive | European Union | Critical infrastructure operators must demonstrate control over where sensitive operational data is processed and stored |
| PDPB / DPDPA | India | Personal data transfers are restricted to government-approved jurisdictions only |
| LGPD | Brazil | Modelled on GDPR; cross-border transfers require either adequacy decisions or appropriate safeguards |
| Privacy Act (Amended) | Australia | Significantly increased penalties; sector-specific restrictions apply to health and financial data transfers |
| IRAP | Australia | Government data must be processed by IRAP-assessed providers; sovereign cloud is commonly mandated |
| PIPL | China | Strict localization rules apply; critical data categories must remain within Chinese borders |
| DSL (Data Security Law) | China | Classifies data by importance; transfer of important data abroad requires a government security assessment |
| PDPA | Singapore | Personal data transferred overseas must receive comparable protection to Singapore's own standards |
| PIPA | South Korea | Cross-border transfers require explicit user consent or adequate protection verification |
| FedRAMP | United States | Cloud services used by federal agencies must meet defined security baselines; sensitive workloads have strict data location requirements |
| HIPAA | United States | Protected health information must be handled under strict access and storage controls regardless of location |
Industry-Specific Data Sovereignty Compliance Requirements.
Different sectors face unique legal hurdles when managing scan data. Understanding these industry-specific mandates is essential to ensure your security testing remains compliant while protecting sensitive, high-stakes information within regional borders.
Financial Services
Banks and fintechs operate under the strictest localization rules, such as those from the RBI or FINMA. These regulators often require that all financial records and related security logs stay in-country. This prevents foreign legal reach from compromising national economic stability or private fiscal data.
Healthcare
Patient privacy is non-negotiable under laws like HIPAA or the EU’s clinical data rules. Security scans in this sector often touch sensitive health records (PHI). Regional storage ensures that this deeply personal data never leaves its protected jurisdiction, preventing massive HIPAA violations and maintaining patient trust.
Government and Public Sector
National security depends on keeping sovereign data away from foreign eyes. The government and public sector require that any tool scanning their infrastructure stores findings on domestic, high-security servers. This isolation is critical to prevent state-sponsored actors from gaining insights into a nation’s digital defenses through off-shore data leaks.
Legal Services
Law firms handle privileged information that must remain confidential to ensure a fair trial. If security scan metadata containing case details moves across borders, it could break attorney-client privilege. Localized storage keeps these sensitive digital trails within the correct legal jurisdiction, protecting the integrity of the firm's work.
Technology Companies Operating Globally
Tech firms scaling across borders must juggle multiple privacy laws simultaneously. By using regional scan controls, these companies can deploy products in new markets like India or the EU faster. It allows them to prove "compliance-by-design" to local auditors, making global expansion much simpler and safer.
Challenges of Managing Data Residency in Cloud Security
Managing data residency in cloud security is challenging because data moves across regions by design. Without clear control, organizations struggle to track where data is processed and stored, increasing compliance and security risks.
1. Lack of Visibility into Data Location
Cloud environments often distribute data automatically across regions. This makes it difficult to know where scan data is being processed or stored, creating gaps in visibility and making compliance tracking harder for security teams.
2. Complex Multi-Region Architectures
Modern applications run across multiple regions for performance and availability. Managing data residency within these distributed setups becomes complex, as data can move between regions without clear boundaries or consistent enforcement of policies.
3. Uncontrolled Cross-Border Data Transfers
Data can be transferred across regions without explicit control in cloud environments. This creates risks of violating data residency and sovereignty requirements, especially when organizations are unaware of how and where data flows.
4. Limited Control in Third-Party Security Tools
Many security tools process data in global infrastructures. If they do not offer regional control, scan data may be stored or analyzed outside approved regions, creating compliance risks even when core systems are properly configured.
5. Evolving Regulatory Requirements
Data protection laws are constantly changing across regions. Keeping up with new data residency and sovereignty requirements is challenging, especially for organizations operating in multiple jurisdictions with different compliance expectations.
How ZeroThreat Enables Regional Data Scanning and Storage Control
ZeroThreat is an AI-driven platform for automated pentesting of web apps and APIs. It offers "Preferred Data Scan and Storage Locations" to give teams total data control.
Users can choose exactly where scans execute and where results are stored. This ensures you meet residency laws while keeping your security operations transparent and trustworthy.
- Strict Compliance Alignment: Meet mandates like GDPR by keeping findings within required geographic boundaries. This simplifies audits while maintaining your organization's high security standards.
- Full Data Residency Governance: Select specific locations for scan execution and storage to ensure findings stay within geographic boundaries. It provides total control over sensitive data without affecting testing depth.
- Sovereign Data Security: Run deep, agentless penetration tests that simulate real attacker behavior. This ensures all scan data is stored exclusively within your designated geographic region.
- Seamless Global Integration: Support consistent security testing across international regions by integrating directly into CI/CD pipelines Respect local data policies while maintaining a high-speed development and deployment workflow.
Every compliance requirement is different. Let us walk you through yours. Contact Us
Conclusion: Taking Control of Data Scan and Storage Locations
Regional data scanning and storage control is no longer a luxury but a fundamental necessity for global compliance. By choosing where your security data is processed and kept, you bridge the gap between deep vulnerability testing and strict residency laws. This localized approach minimizes legal risks while ensuring your security logs remain under your direct jurisdiction.
Managing these requirements manually is complex, but using ZeroThreat makes it effortless. ZeroThreat allows you to select preferred scan and storage locations, ensuring your API and web app testing stays fully aligned with regional mandates. It provides the high-accuracy insights you need while keeping your data footprint secure, compliant, and within your chosen borders.
Frequently Asked Questions
Does the processing location of scan data affect data residency compliance?
Yes, the processing location directly impacts compliance. Data residency requires knowing where data is processed and stored. If scan data is processed in another region, it may fall under different regulations and create compliance risks.
How does regional scan data storage help meet data sovereignty requirements?
Can security scan results be restricted to a specific geographic region?
How does regional storage control reduce cross-border data transfer risk?
What should enterprises look for in a cloud service offering regional scan data storage?
How can regional scan data storage simplify compliance audits?
Explore ZeroThreat
Automate security testing, save time, and avoid the pitfalls of manual work with ZeroThreat.


