All Blogs
How Broken Access Control Is Exploited in Real Apps (Step-by-Step)

Quick Overview: Broken access control is the most exploited vulnerability in web applications today, and most attacks are simpler than you think. This blog covers how attackers exploit authorization flaws step by step, the types of broken access control vulnerabilities, real-world incidents, detection methods, prevention best practices, and how ZeroThreat helps secure your web apps and APIs.
One small mistake in access control can expose your entire application. That is exactly why OWASP Top 10:2025 ranks broken access control as the #1 web application security risk, with 100% of tested applications showing some form of this flaw.
Even more concerning, OWASP's analysis of over 2.8 million applications showed that 94% of them were affected, making broken access control one of the most widespread vulnerabilities in modern systems.
In real applications, attackers do not break-in using complex exploits. They simply take advantage of missing authorization checks. A changed ID, a modified API request, or a direct endpoint call is often enough.
This blog walks you through exactly how attackers use different ways to exploit broken access control vulnerabilities, so you can understand and prevent them in real-world scenarios. We’ll also check out how ZeroThreat’s AI-driven web app pentesting tool can help you detect and fix broken access control 5× faster.
Your app may already have access control gaps. Find out now, for free. Try for $0
ON THIS PAGE
- What is Broken Access Control?
- Understanding Broken Access Control Exploitation with an Example
- Types of Broken Access Control Vulnerabilities
- How Broken Access Control is Exploited by Attackers?
- Top Real-World Incidents of Broken Access Control
- How to Prevent Broken Access Control: Best Practices
- ZeroThreat for Detecting Broken Access Control and Preventing Attacks
- Final Thoughts on Access Control Exploitation
What is Broken Access Control?
Broken access control is a security vulnerability where an application fails to properly enforce user permissions. It currently holds the top position on the OWASP Top 10 list. This vulnerability allows attackers to access sensitive records or perform actions they should not do.
These flaws are particularly dangerous because they are logic-based rather than simple input errors. Research indicates that nearly 94% of applications suffer from these issues. They involve failures in how software manages user roles and data ownership.
The impact often includes unauthorized data modification or total system compromise. Attackers typically exploit these gaps by tampering with URL parameters or targeting hidden APIs. Consistent server-side authorization is the only reliable way to stop these high-impact security breaches.
Understanding Broken Access Control Exploitation with an Example
Broken access control occurs when an application fails to verify if a user has permission to access a specific resource. In many cases, authentication is successful, but authorization logic is missing.
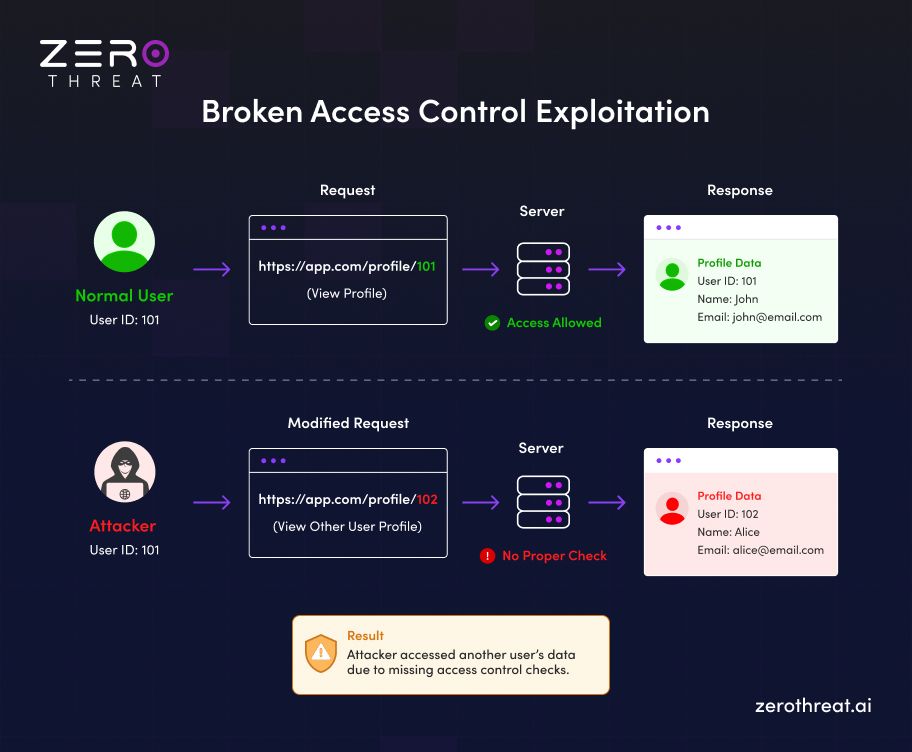
In the provided example, we see how a simple change in a URL can lead to a significant data breach. The exploitation follows a clear, predictable path.
- User 101 requests their own profile. The server validates the session and correctly grants access.
- An attacker changes the ID to 102. This specifically tests for Insecure Direct Object References (IDOR).
- The server processes the request without verifying ownership. It exposes Alice's private information to the attacker.
A normal user views their profile at /profile/101. The server allows this because the identity and the resource match. However, an attacker modifies the URL to /profile/102. If the backend only checks if a user is logged in, it will fail. It ignores the fact that User 101 does not own Profile 102. Consequently, the server sends Alice's private data to the attacker. This missing check results in a successful data breach.
Types of Broken Access Control Vulnerabilities
Broken access control appears in different forms depending on how authorization is implemented in an application. Each type exposes gaps in permission checks, allowing attackers to bypass restrictions and interact with resources they should not access.
IDOR
Insecure Direct Object References occur when applications expose internal object identifiers without proper validation. Attackers can modify IDs in URLs or API requests to access other users’ data. This is one of the most common authorization bypass issues in real applications.
Privilege Escalation
Privilege escalation happens when a user gains higher permissions than intended. This can be vertical, such as a normal user becoming an admin, or horizontal, where users access peer-level accounts. Weak role validation and missing checks often cause this flaw.
Force Browsing
Force browsing allows attackers to access restricted pages by directly guessing or modifying URLs. Applications that rely only on front-end restrictions fail here. Attackers can bypass UI controls and access hidden endpoints or admin panels without proper authorization checks.
Missing Checks
Missing access control checks occur when backend endpoints fail to verify user permissions. APIs may allow sensitive actions like updating or deleting data without validating the requester. This leads to unauthorized actions and exposes critical business logic flaws to attackers.
Token Manipulation
Token manipulation involves tampering with session tokens, cookies, or JWTs to gain unauthorized access. If applications trust client-side data without validation, attackers can modify roles or permissions within tokens to bypass access control mechanisms.
CORS Misconfiguration
CORS misconfiguration allows untrusted domains to interact with secure APIs. If not properly restricted, attackers can perform unauthorized requests from malicious origins. This exposes sensitive endpoints and weakens the overall authorization model in modern web applications.
Real attack simulations. Validated findings. Know your web apps' security right now. Pentest My Web App
How Broken Access Control is Exploited by Attackers?
Attackers exploit broken access control by identifying gaps in authorization logic. They use methods like ID manipulation and token tampering to bypass security boundaries and access unauthorized sensitive data or functions.
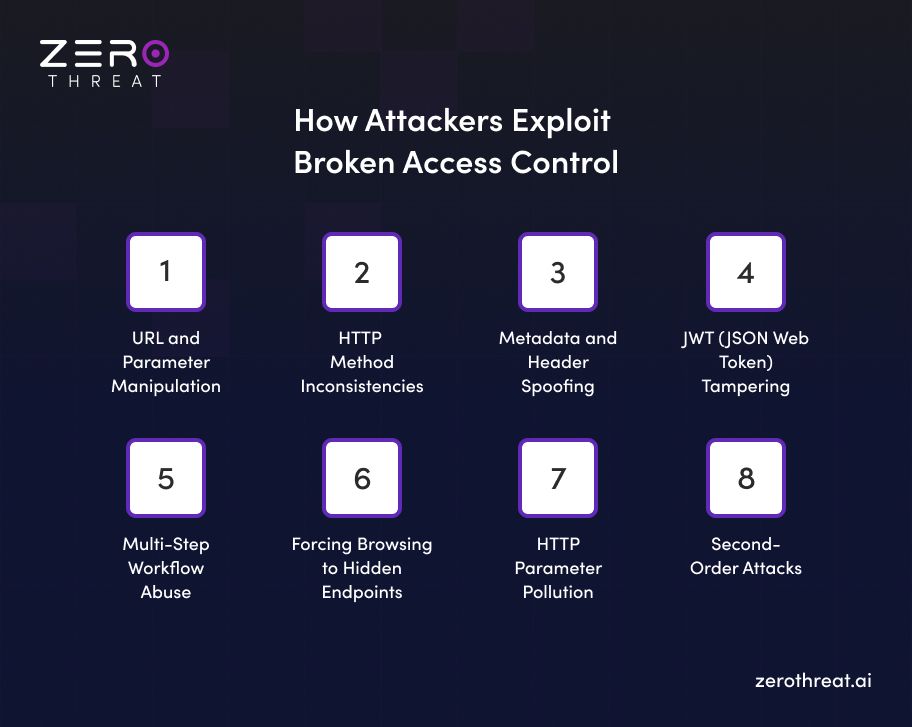
1. URL and Parameter Manipulation
Attackers often start with the simplest method by tampering with the data visible in their browser address bar. This technique involves changing query strings or form parameters to trick the backend into serving data belonging to another user. It is highly effective because many developers mistakenly believe that users will not manually edit URLs. If the server does not verify that the logged-in user actually owns the requested resource, a breach occurs.
- Identify identifiers like user_id or account_no in the URL.
- Increment or decrement those numbers to view other records.
- Capture requests using a proxy to find hidden numeric parameters.
Example: A user logs in and sees the URL example.com/invoice/1001. They change the number to 1002 and successfully view a stranger's private billing statement.
2. HTTP Method Inconsistencies
Many applications apply different security rules based on the HTTP request method used. An attacker might find that a specific endpoint restricts GET requests but fails to protect POST, PUT, or DELETE actions. By simply switching the method, they can perform administrative tasks or modify data without having the required permissions. This happens when authorization is applied inconsistently across different types of requests.
- Try alternative methods like PUT or PATCH on read-only endpoints.
- Use DELETE on a resource ID to see if the server processes it.
- Observe if the application responds differently to various method types.
Example: An API endpoint for /users/profile is restricted for GET requests, but sending a DELETE request to that same URL allows a regular user to delete their account or others' accounts.
3. Metadata and Header Spoofing
Attackers can manipulate the metadata that travels with a request to escalate their privileges. This includes tampering with cookies, hidden form fields, or custom HTTP headers like X-Original-URL. If an application trusts these client-side values to determine a user’s role, it is easy to exploit. Attackers look for flags that indicate admin status or organizational IDs and modify them before the request reaches the server.
- Decode and edit cookies that store role information.
- Inject headers like X-Forwarded-For to bypass IP-based restrictions.
- Look for hidden input fields in the HTML source code.
Example: A user notices a cookie named is_admin=false in their browser. They change the value to true and suddenly gain access to the site's management dashboard.
4. JWT (JSON Web Token) Tampering
Modern apps rely on JWTs for session management, but these tokens are often poorly implemented. Attackers decode these tokens to see the claims inside. If the server does not strictly validate the signature or allows insecure algorithms, the attacker can rewrite their own permissions. This is one of the most common ways to achieve vertical privilege escalation in modern API-driven environments.
- Change the algorithm header to none to bypass signature checks.
- Brute-force weak secret keys used for signing tokens.
- Modify user IDs or role claims within the token payload.
Example: An attacker decodes their JWT and finds "role": "user". They change it to "role": "admin", set the algorithm to none, and the server accepts the unsigned token as valid.
5. Multi-Step Workflow Abuse
In complex processes like a checkout or registration, security checks must exist at every single stage. Attackers exploit "workflow gaps" by skipping intermediate steps or replaying successful requests. If the application only checks permissions at the start of the journey, the attacker can jump directly to the final "success" page or confirmation endpoint to receive services without fulfilling requirements like payment.
- Identify the URLs for the final steps of a transaction.
- Attempt to browse directly to the /success page while a cart is empty.
- Manipulate the order of requests to bypass validation checks.
Example: A user adds an item to their cart and, instead of paying, manually navigates to example.com/order/confirm. The system processes the order because it fails to check if the payment was completed.
6. Forcing Browsing to Hidden Endpoints
Developers sometimes assume that if a link isn't visible in the UI, an attacker cannot find it. This is known as security through obscurity, and it is a major mistake. Attackers use automated tools to guess common administrative paths or analyze client-side JavaScript to find "shadow APIs". These endpoints often lack the robust authorization checks found on the main user-facing pages of the application.
- Use directory brute-forcing tools to find paths like /admin or /config.
- Scrutinize public JavaScript files for references to internal API routes.
- Look for documentation files like swagger.json that list all available endpoints.
Example: An attacker finds a hidden endpoint named /api/v1/debug/dump_users mentioned in a JavaScript file. They access it directly and download a list of all registered user emails.
7. HTTP Parameter Pollution
This advanced technique involves sending multiple parameters with the same name in a single request. Different web servers and frameworks handle these duplicate parameters in various ways. An attacker can use this discrepancy to confuse the application logic. They might provide one valid parameter to pass an initial check and a second malicious one that the backend actually processes for the final action.
- Supply multiple versions of an ID in the same query string.
- Combine URL parameters with POST body parameters to trigger conflicts.
- Observe which value the application prioritizes during processing.
Example: An attacker sends a request like /transfer?amount=10&to=friend&to=attacker. The security filter sees the first to value, but the database uses the second one to complete the transfer.
8. Second-Order Attacks
Second-order vulnerabilities occur when an attacker’s input is processed in a secondary context where security checks are weaker. This is often seen in session poisoning or internal API calls. Many apps use a middleware that authenticates to an internal service using a single, globally shared admin token. If the internal service does not perform its own checks, it will serve whatever the middleware asks for.
- Use "Forgot Password" to overwrite session email.
- Inject paths into internal middleware requests.
Example: An attacker might use the "Forgot Password" page to enter a victim's email while still logged in. If the app stores that email in the current session without forcing a logout, the attacker can navigate back to their account page. This results in a full account takeover without ever knowing the victim's password.
Top Real-World Incidents of Broken Access Control
Broken access control is not just a theoretical risk. It has been a key factor behind several major data breaches. These incidents show how weak authorization checks and misconfigured access can expose sensitive data at scale.
Kia’s Web Portal Vulnerability (2024)
In June 2024, security researchers discovered that Kia's dealer portal could be exploited to control any vehicle equipped with remote hardware in under 30 seconds, regardless of whether it had an active Kia Connect subscription.
An attacker could use only a license plate number to retrieve a vehicle owner's personal information, replace their email address, and add themselves as the primary account holder, then send arbitrary remote commands to the vehicle without the owner's knowledge. The root cause was missing server-side authorization checks on dealer-level API endpoints.
Snowflake Customer Data Breach (2024)
Between April and June 2024, the threat group UNC5537 compromised over 100 Snowflake customer environments by using stolen credentials to bypass authentication. None of the breached accounts had multi-factor authentication enabled, allowing attackers to log in using only a username and password.
The major victims included AT&T, Ticketmaster, and Advance Auto Parts, collectively impacting hundreds of millions of individuals. The breach showed how absent access controls and poor credential hygiene can collapse an entire cloud security perimeter.
MOVEit Transfer Data Breach (2023)
In May 2023, a critical SQL injection vulnerability in Progress Software's MOVEit Transfer application was exploited by the Cl0p ransomware group, leading to unauthorized access across more than 2,700 organizations and exposing the personal data of approximately 93 million individuals.
The flaw allowed unauthenticated attackers to interact directly with MOVEit's database and execute commands beyond the software's intended functionality, bypassing all authorization controls in place. High-profile victims included the BBC, British Airways, and multiple U.S. government agencies.
LinkedIn API Breach (2021)
In 2021, attackers exploited LinkedIn's API to collect data from approximately 700 million user accounts by combining publicly available information with private details made accessible through improper API access controls.
The attacker connected this data with other API sources to build a large dataset of personal information, which was then sold online. The attack exposed data for roughly 90% of LinkedIn's user base and forced the company to re-evaluate its entire API authorization scheme.
Validate your security posture against real-world attacks with 98.9% accuracy. Run a Pentest
How to Prevent Broken Access Control: Best Practices
Preventing broken access control requires a structured approach to authorization. Strong access control policies, consistent validation, and continuous testing help reduce unauthorized access risks and protect sensitive application data.

Implement Least Privilege Principle
Grant users only the minimum access levels required to perform their specific roles. This strategy limits the potential damage if an account becomes compromised by a malicious actor. Regularly reviewing permissions ensures that excessive rights are removed as soon as they are no longer necessary.
Enforce Deny by Default
Adopt a strict policy where all access is blocked unless it is explicitly permitted by the system. This baseline protection prevents unauthorized users from discovering or exploiting hidden endpoints that lack specific rules. It creates a failsafe environment that protects sensitive resources by default.
Validate Server-Side Controls
Always perform authorization checks within your server side logic instead of relying on client side UI restrictions. Attackers can easily bypass browser based limits by tampering with request parameters or direct API calls. Server side validation ensures every action is verified against real permissions.
Centralize All Authorization Logic
Avoid scattering access rules throughout your application's codebase to prevent inconsistent enforcement and dangerous security gaps. Using a unified framework ensures that every request follows the same rigorous validation process. Centralizing these controls makes it much easier to audit and manage complex roles.
Conduct Audits and Pentesting
Routinely perform security audits and automated pentesting to identify logic flaws before they reach production. Modern DAST tools scan live applications to find exposed endpoints that static analysis often misses. Combining automated scans with manual reviews provides the most comprehensive defense possible.
ZeroThreat for Detecting Broken Access Control and Preventing Attacks
Most security tools tell you a vulnerability exists. ZeroThreat tells you exactly what to do about it.
ZeroThreat is an AI-driven, automated penetration testing platform built to detect broken access control vulnerabilities across web applications and APIs. It continuously tests authorization logic, maps exposed endpoints and identifies privilege escalation paths that manual testing often misses.
What makes ZeroThreat different is the remediation layer. Every detected vulnerability comes with AI-powered, context-aware guidance, so your developers know precisely what needs fixing and how to fix it.
For teams looking to stay aligned with standards - OWASP Top 10 and CWE, other compliance standards, and secure their web apps from attacks, ZeroThreat provides structured coverage over 130,000 vulnerabilities, making it a reliable choice for continuous security testing at scale.
Every breach starts with a missed vulnerability. Talk to us before that happens to you. Contact Us
Final Thoughts on Access Control Exploitation
Broken access control remains one of the most exploited weaknesses in modern applications. Attackers focus on simple gaps like missing checks, exposed APIs, and weak role validation to gain unauthorized access and control sensitive actions.
Preventing access control exploitation issues requires a disciplined approach to authorization. Enforcing the least privilege, validating every request on the server, and centralizing access logic reduces risk significantly. Continuous testing also plays a critical role in identifying hidden flaws before attackers can exploit them.
ZeroThreat’s AI-powered automated pentesting tool simplifies this with real exploit validation. It detects access control vulnerabilities in real workflows and provides clear remediation guidance. This helps teams fix issues faster and maintain strong, consistent authorization across applications.
Frequently Asked Questions
How do attackers exploit access control in real applications?
Attackers look for endpoints that do not validate who is making the request. They manipulate user IDs in URLs, switch HTTP methods, tamper with tokens, and probe for unprotected admin routes. If the server trusts the request without verifying authorization, access is granted.
How do hackers bypass role-based access control?
How is broken access control exploited in APIs?
How do I test access control like a penetration tester?
How do modern apps fail in authorization checks?
Explore ZeroThreat
Automate security testing, save time, and avoid the pitfalls of manual work with ZeroThreat.


