All Blogs

Quick Overview: Agentic AI is redefining how application security testing works. This guide covers what agentic AI is, how it finds vulnerabilities traditional scanners miss, the attacks it can simulate, and how it compares to traditional AI pentesting. It will also cover how to integrate agentic AI pentesting into your DevSecOps pipeline and why it is the next-gen security solution.
The way applications get attacked has changed. Threats are faster, more targeted, and increasingly automated. Yet many security teams are still relying on annual pentests and rule-based scanners that were never designed to keep up with how modern applications are built or how they get breached.
This is the gap agentic AI was built to close.
According to Gartner, by 2027, more than 40% of agentic AI deployments will involve security-related workflows. IBM's Cost of a Data Breach Report found that organizations using AI and automation in security identified breaches 108 days faster than those that didn't. These numbers make it clear the industry is moving, and the teams adopting intelligent, autonomous testing are pulling ahead.
Agentic AI in application security doesn't just scan. It reasons, plans, and acts autonomusly. It simulates the way a real attacker approaches your application, chains multi-step exploits, tests business logic, validates findings, and does all of this continuously, without waiting for someone to schedule a test.
This guide covers everything you need to understand about application security with agentic AI penetration testing. We’ll cover what agentic AI is, how it works, what it can find, how it compares to traditional methods, and how to integrate it into your existing security workflow.
If you're serious about keeping your applications secure in 2026, this is where to start.
Stop guessing where your vulnerabilities are. Let agentic AI find them for you. Try for $0
ON THIS PAGE
- What is Agentic AI in Application Security?
- How Agentic AI Finds Vulnerabilities Traditional AI Scanners Miss
- How Agentic AI Pentesting Works: From Discovery to Exploitation
- Traditional AI vs. AI Agents vs. Agentic AI
- What Attacks Can Agentic AI Simulate?
- Integrating Agentic AI into DevSecOps Pipeline
- Compliance and Audit-Readiness with Agentic AI Testing
- Is Agentic AI Security Testing Safe? How ZeroThreat Performs Pentesting
- The Future of Application Security: Why Agentic AI Wins
What is Agentic AI in Application Security?
Agentic AI in application security refers to autonomous AI systems that can independently discover, test, and validate vulnerabilities in web applications. Unlike traditional scanners, agentic AI pentesting tools can reason, plan, and execute multi-step security testing without constant human input.
In practice, agentic AI behaves like a security tester that continuously explores an application. It crawls, interacts, and adapts based on context, enabling it to uncover complex issues such as business logic flaws and authentication weaknesses that static scanners often miss.
What makes it powerful is its ability to move beyond detection into action. Agentic AI can simulate real attacks, validate exploits, and refine its approach using feedback loops. This creates a continuous, AI-driven security testing process that aligns with modern DevSecOps workflows.
How Agentic AI Finds Vulnerabilities Traditional AI Scanners Miss
Agentic AI finds vulnerabilities by mimicking thinking and acting like a real attacker. It does not rely on fixed rules. It adapts, chains actions, and validates impact, which helps uncover deeper and more realistic security risks.
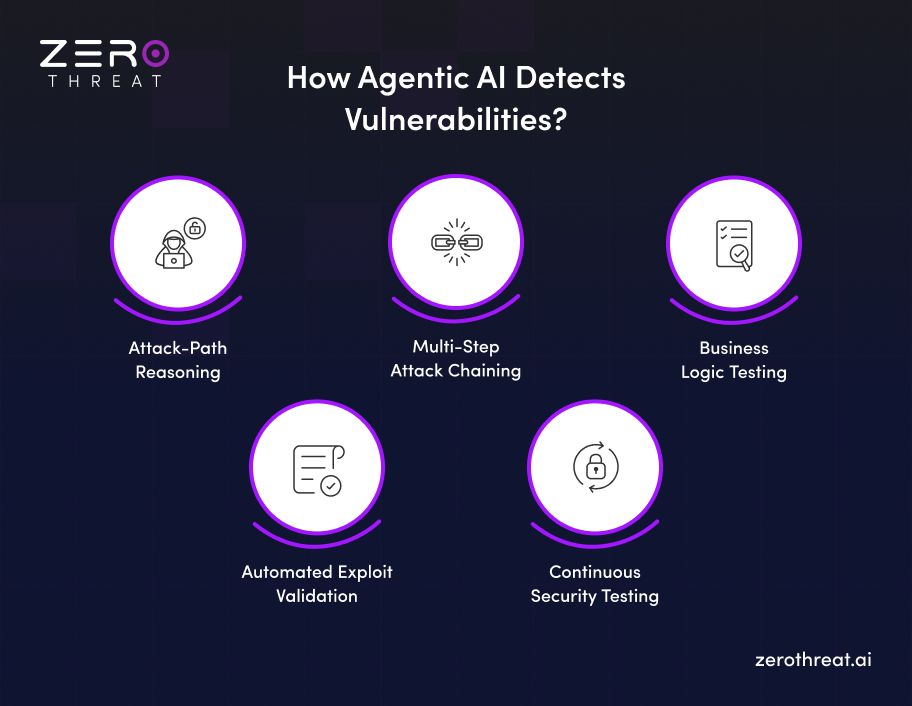
Attack-Path Reasoning
Agentic AI does not follow predefined test cases. It breaks down goals into steps, plans, actions, and adjusts based on application responses. This allows it to explore real attack paths instead of isolated issues. Unlike traditional scanners, it maintains context across sessions and continuously refines its approach.
Multi-Step Attack Chaining
Traditional tools test vulnerabilities in isolation. Agentic AI connects multiple weaknesses into a single attack chain. It can move from one flaw to another, such as combining security misconfigurations with access control issues. This mirrors how real attackers escalate privileges and achieve deeper system compromises.
Business Logic Testing
Business logic flaws are hard to detect because they depend on application behavior. Agentic AI interacts with workflows like a real user. It tests edge cases, abuse scenarios, and unintended flows. This helps uncover issues in transaction, authentication, and authorization logic that rule-based scanners usually miss.
Automated Exploit Validation
Most scanners report potential vulnerabilities without proof. Agentic AI goes further by attempting exploitation. It validates whether the vulnerability is really exploitable and shows its impact. This reduces false positives and gives security teams clear, actionable findings instead of theoretical risks.
Continuous Security Testing
Agentic AI runs continuously instead of at fixed intervals. It tests applications as they change, especially in CI/CD environments. This ensures new vulnerabilities are identified early. Continuous validation improves coverage and keeps security aligned with modern, fast-moving SDLCs.
Traditional scanners miss what attackers exploit. Switch to agentic AI pentesting now.Pentest My Application
How Agentic AI Pentesting Works: From Discovery to Exploitation
Agentic AI pentesting follows a structured yet adaptive process. It moves from discovering attack surfaces to validating real exploits. Each step is guided by reasoning, context awareness, and continuous learning.
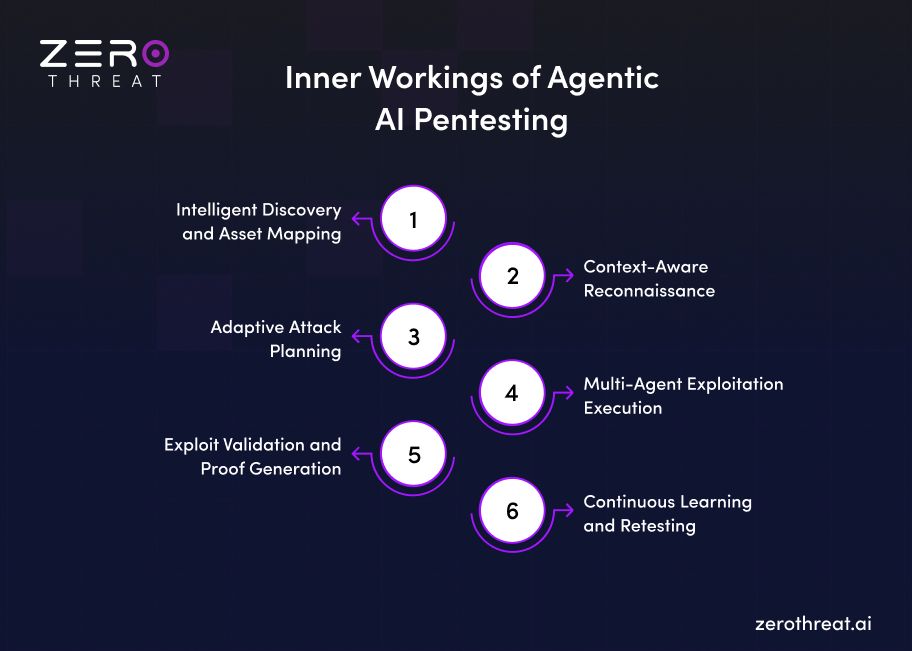
Step 1: Intelligent Discovery and Asset Mapping
Agentic AI starts by crawling the application to identify endpoints, APIs, and entry points. It builds a contextual map of the attack surface. Unlike static scanners, it understands technologies, frameworks, and authentication states to create a focused testing strategy tailored to your application.
Step 2: Context-Aware Reconnaissance
Once the surface is mapped, the AI gathers deeper insights. It analyzes responses, session behavior, and application logic. It maintains an authentication context and adapts its exploration. This allows it to uncover hidden paths and sensitive workflows that traditional tools often fail to explore.
Step 3: Adaptive Attack Planning
Agentic AI does not run predefined scripts. It creates a dynamic attack plan based on discovered patterns. It prioritizes high-risk areas and selects appropriate attack techniques. This planning mimics how a human tester thinks, focusing on realistic exploitation paths instead of isolated vulnerability checks.
Step 4: Multi-Agent Exploitation Execution
Specialized AI agents execute attacks in parallel. Each agent focuses on specific vulnerability classes such as injection, authentication bypass, or API abuse. These agents share context and refine their actions in real time. This coordinated approach increases coverage and helps identify complex, chained vulnerabilities.
Step 5: Exploit Validation and Proof Generation
Instead of reporting assumptions, agentic AI attempts to validate each finding. It confirms whether a vulnerability is exploitable and captures proof. This ensures results are actionable and reduces false positives, allowing security teams to focus only on real, verified risks.
Step 6: Continuous Learning and Retesting
Agentic AI does not stop after one test cycle. It learns from previous results and improves its strategies. It continuously retests applications as they evolve, ensuring new vulnerabilities are identified early. This enables continuous security testing aligned with modern DevSecOps practices.
Traditional AI vs AI Agents vs Agentic AI
| Aspect | Traditional AI | AI Agents | Agentic AI |
|---|---|---|---|
| Primary role | Detects, classifies, predicts, or recommends | Executes a defined task autonomously | Achieves broader security goals through reasoning and action |
| Decision model | Narrow and model-driven | Task-specific and workflow-bound | Goal-driven, adaptive, multi-step decision making |
| Context awareness | Limited to specific inputs | Uses task-level context | Uses full application, workflow, and environmental context |
| Tool usage | Minimal or indirect | Uses one or more integrated tools | Orchestrates multiple tools and systems dynamically |
| Planning ability | Minimal | Limited planning within scope | Advanced multi-step planning and replanning |
| Adaptability | Low to moderate | Moderate within defined tasks | High adaptability based on feedback and changing conditions |
| Application in security | Alert scoring, anomaly detection, recommendations | Automated triage, ticket enrichment, evidence collection | End-to-end pentesting, exploit validation, attack simulation |
| Human involvement | Moderate supervision required | Moderate oversight for workflows | Higher oversight for critical and high-impact actions |
What Attacks Can Agentic AI Simulate?
Agentic AI simulates sophisticated, multi-stage attacks by leveraging autonomous reasoning to coordinate tools and exploit complex vulnerabilities. Here are the types of attacks agentic AI can simulate:
Advanced Reconnaissance
Agentic AI maps your full attack surface before testing begins, the way a skilled attacker would.
- Hidden endpoints, exposed parameters, and technology fingerprints are all discovered and catalogued.
- Component relationships are analyzed to build a realistic picture of exploitable entry points.
- High-value targets are prioritized based on context, not just surface-level visibility.
Exploitation and Tool Misuse
Once weaknesses are identified, agentic AI attempts to exploit them using intelligent, context-aware techniques.
- Targeted payloads are crafted based on application behavior rather than fixed signature lists.
- Discovered vulnerabilities are tested for chaining potential to reveal higher-impact exploit paths.
- Legitimate application features are probed for misuse to expose logic-level security gaps.
Privilege Escalation and Persistence
Agentic AI doesn't stop at initial access. It tests how far an attacker could go once inside.
- Horizontal and vertical privilege escalation is attempted across different user roles and access levels.
- Session persistence is tested to check whether elevated access can be maintained without triggering detection.
Automated Ransomware and Data Exfiltration
Agentic AI simulates the behaviors that follow a successful breach, helping you understand downstream risk.
- Sensitive data access, aggregation, and movement are tested against your existing security controls.
- Potential staging and exfiltration paths are identified before a real attacker can find them.
- Detection and blocking capabilities are validated against simulated exfiltration attempts in real time.
Multi-Agent System Attacks
As AI systems become part of your stack, they introduce new attack surfaces that require specialized testing.
- Prompt injection and input tampering are used to test whether AI agents in your application can be manipulated.
- Trust boundary violations between agents are checked to assess cross-agent compromise risk.
- Coordinated attack scenarios are simulated to expose weaknesses that span multiple points in an agentic workflow.
Continuous agentic AI security testing at a price that matches your budget.Check Out Pricing
Integrating Agentic AI into DevSecOps Pipeline
Security testing no longer belongs at the end of the development cycle. Integrating agentic AI into your DevSecOps pipeline means vulnerabilities get caught early, automatically, and continuously.
Approach to Integrate Agentic AI into DevSecOps Pipeline
- Embed agentic AI into CI/CD workflows: Integrate AI agents directly into build and deployment pipelines. This allows continuous security testing during code commits, builds, and releases, improving early vulnerability detection and reducing security bottlenecks.
- Start with focused security use cases: Begin with specific use cases such as API security testing or vulnerability validation. This helps teams validate impact quickly and scale agentic AI adoption without disrupting existing DevSecOps processes.
- Enable multi-agent orchestration across tools: Use agent orchestration models where multiple AI agents collaborate across scanners, CI tools, and infrastructure systems. This improves coverage and allows coordinated testing, validation, and remediation across environments.
- Implement policy-driven governance: Define clear policies for how agents operate, access systems, and take actions. Strong governance ensures safe automation, auditability, and compliance across security workflows and infrastructure.
- Integrate continuous feedback and learning loops: Enable agents to learn from previous test results, code changes, and incidents. This improves detection accuracy and helps adapt security testing strategies based on real application behavior over time.
- Ensure unified visibility across systems: Centralize logs, telemetry, and agent decisions into a single view. This helps security teams monitor actions, validate outcomes, and maintain control over autonomous testing processes across the pipeline.
- Maintain human-in-the-loop oversight: Keep security teams involved in critical decisions such as exploit validation and remediation approval. This ensures accountability while allowing agentic AI to handle repetitive and scalable security testing tasks effectively.
Compliance and Audit-Readiness with Agentic AI Testing
Agentic AI testing improves compliance by turning security validation into a continuous, evidence-driven process. It helps organizations generate audit-ready reports, enforce policies, and maintain visibility across application security workflows.
Agentic AI enables continuous compliance monitoring instead of periodic checks. It tests applications in real time and validates vulnerabilities with proof. This reduces audit gaps and improves traceability. Studies show automation can reduce compliance audit effort by up to 40 percent through continuous validation.
A key advantage is audit-ready evidence generation. Agentic AI produces reproducible findings, detailed logs, and validation steps for each vulnerability. These records support regulatory requirements such as ISO, SOC 2, and data protection standards by providing clear, verifiable security outcomes.
Strong governance and control mechanisms are essential. Agentic AI systems enforce policies, track access, and maintain detailed audit trails across workflows. This ensures accountability, supports human oversight, and aligns autonomous security testing with enterprise compliance and audit expectations.
Is Agentic AI Security Testing Safe? How ZeroThreat Performs Controlled Pentesting
Agentic AI security testing is safe when it operates within defined boundaries, controlled environments, and human oversight. By using bounded reasoning, these systems prevent out-of-scope actions. Modern platforms ensure that autonomous agents validate vulnerabilities without disrupting live production environments or compromising sensitive data integrity.
ZeroThreat’s agentic AI penetration testing ensures safe security testing by using a controlled architecture that limits agent behavior to specific, user-defined boundaries. The platform utilizes intelligent reasoning to explore complex application paths, such as business logic and authenticated flows, without the risk of unchecked or destructive autonomy.
Here is how ZeroThreat ensures controlled penetration testing:
- Bounded Testing Actions: The system uses precise and bounded testing actions to strictly follow the rules of engagement. This prevents agents from targeting unauthorized assets or interacting with out-of-scope hosts.
- Customer-Managed AI Models: ZeroThreat allows organizations to use their own AI models to maintain total data control. This ensures that all reasoning and sensitive information remain governed by internal security policies.
- Proof-Based Exploit Validation: Agents use proof-based validation to confirm vulnerabilities through safe, real-time simulations. This method eliminates noisy false positives while providing audit-ready evidence without causing production downtime.
Have questions about integrating agentic AI into your pipeline? Let's help you out.Get in Touch
The Future of Application Security: Why Agentic AI Wins
Application security has always been a race between defenders and attackers. Agentic AI finally gives defenders the speed advantage. It tests continuously, adapts intelligently, covers attack surfaces traditional scanners miss, and delivers verified findings that teams can act on immediately.
The shift from periodic testing to continuous, autonomous security is no longer a future concept. It is happening now. Organizations that adopt agentic AI into their DevSecOps workflows are reducing exposure windows, improving compliance posture, and catching vulnerabilities before attackers ever get the chance.
ZeroThreat is built exactly for this. Its agentic AI pentesting tool combines autonomous attack simulation, authenticated testing, and exploit validation into one controlled, safe, and scalable solution. If you are ready to move beyond outdated scanners, run your first agentic pentesting for free!
Frequently Asked Questions
What is agentic AI and how is it used in security testing?
Agentic AI is an autonomous system that plans and executes complex security tasks without constant human direction. In security testing, it uses independent reasoning to explore applications, discover deep vulnerabilities, and validate real attack paths. This technology transforms testing from simple scanning into goal-directed, adaptive simulations.
Can agentic AI test authentication and authorization flaws?
Is agentic AI accurate enough to replace human pentesters?
Can agentic AI reduce false positives in security testing?
How does agentic AI find security vulnerabilities automatically?
Agentic AI vs traditional security scanners; what's the difference?
Can agentic AI detect business logic vulnerabilities?
How does agentic AI integrate with CI/CD for security?
Why choose ZeroThreat for agentic AI pentesting?
Explore ZeroThreat
Automate security testing, save time, and avoid the pitfalls of manual work with ZeroThreat.