All Blogs
How ZeroThreat Detects API Vulnerabilities Beyond Swagger Files
Quick Overview: Relying solely on Swagger files leaves dangerous API security blind spots. Discover how Shadow and Zombie APIs create hidden risks outside your Swagger documentation. Learn how ZeroThreat identifies these vulnerabilities using AI-powered attack simulation, providing a complete view of your API attack surface beyond the static specifications.
APIs are now the most targeted attack surface, yet most teams still trust documentation for security. Recent industry reports show that over 80% of web traffic is API-driven, making undocumented and poorly secured APIs a prime target for attackers.
The key reason behind APIs being a target is that most security teams don’t check through endpoints that weren’t documented in Swagger files and OpenAPI. That makes their test unreliable. Swagger files look complete, but attackers see a much larger and more exposed API surface.
Swagger documentation explains how APIs should work. It does not show how APIs actually behave under abuse. It can lead to missed vulnerability detection in Shadow APIs and Zombie APIs. Plus, the misconfigurations and business logic don’t get tested when running a Swagger vulnerability scan.
This is where API vulnerability detection must go beyond documentation. In this blog, we break down how ZeroThreat’s API pentesting tool discovers hidden APIs, validates real exploit paths, and uncovers security gaps that Swagger-based testing misses.
Elevate your API security with ZeroThreat’s AI-driven pentesting. Get Started FREE
On This Page
- Why Swagger Files are Not the Complete API Security You Need
- Common API Vulnerabilities Hidden Outside Swagger Files
- The Vulnerabilities Swagger Files Can't See: Shadow and Zombie APIs
- How ZeroThreat Detects Vulnerabilities Beyond Swagger Files
- Final Thoughts
Why Swagger Files are Not the Complete API Security You Need
Swagger files do not reflect the real API attack surface. They document what teams believe is exposed, not what is actually reachable in a live environment. But from a security perspective, it is incomplete.
Here’s why...
Swagger documentation depends on manual updates: As APIs evolve, endpoints change, new routes are added, and old ones are rarely removed. Over time, the Swagger API documentation drifts away from reality. This creates undocumented endpoints that attackers can discover, but security teams often miss.
Swagger cannot detect runtime vulnerabilities: Issues such as broken authentication, weak authorization, and business logic flaws only appear when APIs are running. API security testing requires observing real behavior, not static definitions. Swagger was never designed to identify API vulnerabilities at this level.
Swagger misses zombie and shadow APIs: Zombie APIs are deprecated endpoints that remain active. Shadow APIs are created without formal approval or documentation. Neither appears in swagger documentation for APIs, yet both significantly expand the attack surface and are common targets for exploitation.
In simple terms, Swagger files can’t show the complete picture of API vulnerabilities. Relying on it alone leads to blind spots in API vulnerability detection, increases risk from API sprawl, and leaves organizations exposed to shadow and zombie APIs. Swagger is a useful starting point, but it should never define the boundaries of your API security.
Common API Vulnerabilities Hidden Outside Swagger Files
The common API vulnerabilities hidden outside Swagger files exist because real APIs expose more than what the documentation shows. Here are the key security issues that would be exposed by testing only Swagger files.
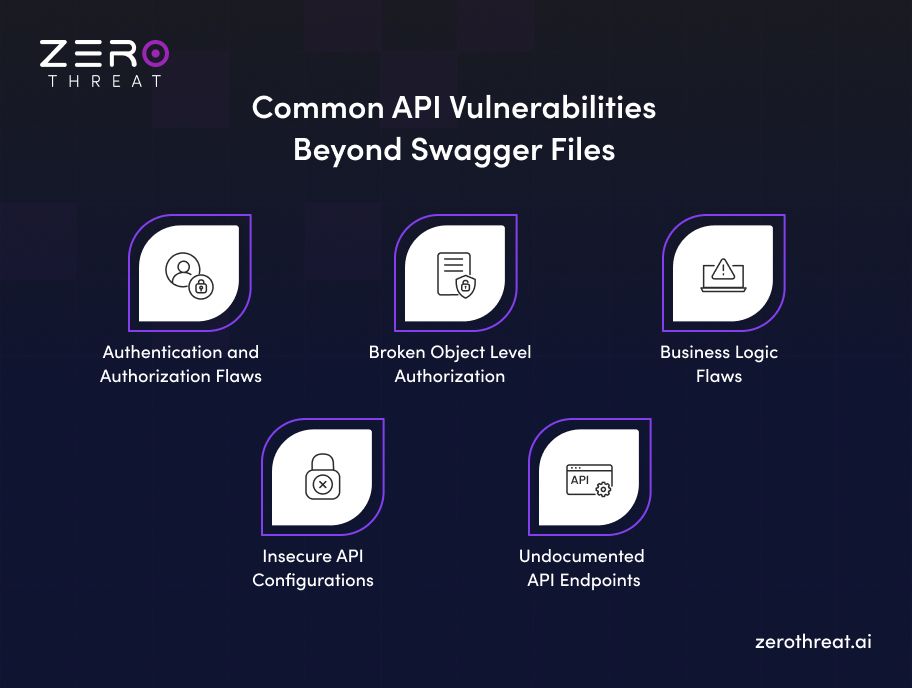
Authentication and Authorization Flaws
Authentication and Authorization flaws occur when APIs fail to properly verify who the user is or what they are allowed to access. Swagger API documentation may show authentication rules, but real APIs often behave differently at runtime. If you miss token validation, or have weak role checks, it can create security gaps that attackers exploit
Broken Object Level Authorization (BOLA)
BOLA happens when APIs allow users to access objects they don’t own. Swagger files may define the endpoint structure but not ownership logic. Attackers simply change object IDs to access other users’ data. This is one of the most common API vulnerabilities missed by Swagger-based testing.
Business Logic Flaws
Business logic flaws exist when APIs behave in ways developers did not expect. Swagger documentation explains how APIs should work, not how they actually respond under abuse. Attackers chain valid requests to bypass limits, skip steps, or abuse workflows. These flaws only appear during real API interaction.
Insecure API Configurations
Insecure configurations expose APIs through open methods, verbose error messages, or weak rate limits. Swagger API testing does not validate production settings. Plus, differences between environments often introduce security gaps. Attackers rely on these security misconfigurations to discover and exploit APIs beyond Swagger files.
Undocumented API Endpoints
Undocumented endpoints are APIs that exist but are never added to Swagger documentation. These often include internal or quickly deployed API endpoints. Since they are missing from the API Swagger file, they bypass standard testing. A hacker can actively search for these hidden paths because they are rarely secured properly.
Secure your API endpoints from attackers by identifying security flaws with 98.9% accuracy. Run API Pen Tests
The Vulnerabilities Swagger Files Can't See: Shadow and Zombie APIs
Shadow and zombie APIs expose real vulnerabilities that Swagger files never capture. These undocumented endpoints expand the API attack surface and are often weakly secured, making them easy targets for attackers. Let’s understand both of these APIs and why they can be a reason behind potential threats.
What are Shadow APIs?
Shadow APIs are endpoints created outside formal development and security processes. They often appear during quick fixes, internal experiments, or urgent releases. Since they are never added to Swagger API documentation, they remain invisible during standard swagger API testing.
These APIs are missed because Swagger only reflects what teams document intentionally. Shadow APIs live in production but outside the API Swagger file. As a result, they bypass API security testing and often run with weak authentication or no access controls.
What are Zombie APIs?
Zombie APIs are old or deprecated endpoints that were never properly removed. They stay live even after newer versions replace them. Swagger documentation rarely includes these endpoints because teams assume they are no longer in use.
They are missed during swagger testing because they no longer appear in swagger documentation for APIs. Yet attackers can still access them. Since zombie APIs are outdated, they often contain known vulnerabilities and outdated security logic.
Why Shadow and Zombie APIs are Dangerous?
Shadow and zombie APIs are dangerous because they expose hidden attack paths that security teams don’t monitor or protect. These undocumented APIs expand the real attack surface and allow attackers to bypass standard API security controls.
The Shadow and zombie APIs can create a security loophole because they can...
- Bypass Swagger-based API security testing and documentation
- Run without proper authentication or authorization controls
- Expose sensitive data through undocumented API endpoints
- Increase risk due to uncontrolled API sprawl
- Remain unmonitored, unlogged, and unpatched in production
How ZeroThreat Detects Vulnerabilities Beyond Swagger Files
ZeroThreat detects vulnerabilities beyond Swagger files by using AI-powered attack simulation to analyze runtime behavior and business logic flaws. It goes beyond traditional signature-based scanning to find issues specific to an application's unique implementation.
ZeroThreat’s automated pentesting tool secures your application beyond Swagger files by:
- Discovering Undocumented "Shadow" APIs: Its AI-powered crawler actively maps your entire running application. It finds live endpoints that developers may have created but never added to the official Swagger documentation, closing a major visibility gap.
- Identifying Runtime & Business Logic Flaws: As a Dynamic Application Security Testing (DAST) tool, it tests your application in its running state. This helps find complex business logic flaws and configuration issues that static API specs can't reveal.
- Prioritizing Exploitable Risks: An AI engine analyzes findings to filter out theoretical flaws. It focuses on vulnerabilities that are actually reachable and dangerous, drastically reducing false alarms and alert fatigue.
- Scanning Continuously with Every Code Change: By integrating into your
CI/CD pipeline (like GitHub Actions), it automatically tests every update. This catches security gaps the moment new code or a forgotten "zombie" API is deployed.
Get help discovering shadow and zombie APIs in your environment. Contact Us
Final Thoughts: Securing APIs Outside Swagger Files
Swagger files are useful, but they were never meant to define API security boundaries because real API risks live beyond documentation. Undocumented endpoints, shadow APIs, zombie APIs, and runtime flaws create blind spots that attackers actively exploit.
Effective API vulnerability detection requires testing how APIs behave in production, not how they are described. Authentication gaps, authorization failures, business logic flaws, and insecure configurations only surface when APIs are tested from an attacker’s point of view.
ZeroThreat’s API penetration testing tool addresses this gap by discovering real API exposure beyond Swagger files. It identifies hidden APIs, validates exploitable risks, and continuously tracks API sprawl. This helps teams move from documentation-based assumptions to real, reliable API security.
Frequently Asked Questions
Why is relying only on Swagger or OpenAPI documentation risky for API security?
Relying only on Swagger is risky because it shows intended API design, not real exposure. Undocumented endpoints, runtime flaws, and misconfigurations stay invisible, leaving an open gate for attackers to exploit the application vulnerabilities.
How do undocumented or shadow APIs increase breach risk for organizations?
Can ZeroThreat detect vulnerabilities even when no Swagger file exists?
How does ZeroThreat validate whether a discovered vulnerability is actually exploitable?
How does ZeroThreat identify hidden or shadow APIs that Swagger documentation misses?
Explore ZeroThreat
Automate security testing, save time, and avoid the pitfalls of manual work with ZeroThreat.