
All Blogs
Automated API & Asset Discovery: Identifying Shadow and Zombie APIs at Scale
Quick Overview: Web applications expose more APIs than teams realize, creating hidden risks across cloud and CI/CD environments. This blog explains how automated API and asset discovery uncovers shadow and zombie APIs at scale, reduces security blind spots, and strengthens governance.
Modern web applications are highly dependent on APIs, with APIs handling over 80% of today’s web traffic. That means even a single hidden endpoint can quietly expand the attack surface without anyone noticing.
As applications scale, the number of APIs grows as well. Some APIs are well documented, while others are forgotten, deprecated, or never recorded at all. These shadow and zombie APIs create blind spots that traditional API security tools often miss.
Security issues rarely start with known APIs. They start with API endpoints that are undocumented or hidden. Undocumented APIs, inactive services, and exposed internal endpoints give attackers easy entry points, especially when authentication, monitoring, or ownership is unclear.
This is where automated API and asset discovery become critical. By continuously scanning web API in real environments, security teams can get a complete view of their security posture. It allows them to know the unknown risks, fix vulnerabilities, and ensure security against cyber-attacks.
Start discovering shadow and hidden APIs before attackers do. Start Free Scan
On This Page
- What is Automated API & Asset Discovery?
- Understanding Documented and Undocumented APIs
- Risk of Incomplete API Discovery in Web Applications
- Importance of Asset and API Discovery for Security
- How ZeroThreat Automates API Discovery
- API Discovery Best Practices for Security Teams
- Summing Up
What is Automated API & Asset Discovery?
Automated API & asset discovery is the process of automatically finding all APIs, endpoints, and related assets across a website without relying on manual documentation. It gives security teams a real, up-to-date view of what APIs exist, where they run, and how they are exposed.
In modern applications, APIs change fast, and new endpoints are added frequently. Some never even make it into documentation. Automated API discovery solves this by continuously discovering API endpoints as they appear in production, staging, and CI/CD environments.
Unlike manual inventories or Swagger-based tracking, automated API & asset discovery works in real conditions. It identifies documented and undocumented API endpoints. It also detects hidden, shadow, and zombie APIs that expand the API attack surface without visibility.
This approach combines automated endpoint discovery with automated asset discovery. It builds a live API asset inventory instead of a static list. As applications change, the inventory updates automatically. That is why continuous API discovery is critical for security teams.
You cannot protect APIs you do not know exist. Automated API & asset discovery helps eliminate API blind spots, reduce unknown exposure, and support accurate API attack surface discovery.
In short, automated API & asset discovery gives teams visibility over every API, whether it is documented or undocumented. It turns API sprawl into a manageable process within an organization for security against cyber-attacks.
Understanding Documented and Undocumented APIs
APIs across modern applications are not always visible or tracked the same way. Some are well-known and actively maintained, while others exist in the background as systems change. This mix shapes the foundation of the API attack surface. To secure your web app and APIs, it’s crucial to discover both documented and undocumented APIs.
But what exactly are they? Let’s take a closer look at both.
Documented APIs
Documented APIs are APIs that are officially created, tracked, and shared within an organization. They are usually defined in API specifications like Swagger or OpenAPI and are known to development and security teams. These APIs follow planned release cycles and change through controlled processes. Security teams know what they are, where they run, and how they are supposed to behave.
From a security perspective, documented APIs are far easier to control. You can perform a vulnerability scan on them, enforce authentication, and track changes over time. They are part of API governance, so teams understand their purpose and risk. However, good documentation must stay up to date.
Because documented APIs are part of official workflows, they typically receive security checks before deployment. But documentation alone doesn’t guarantee protection. Teams must still validate that the API behaves as expected in the real world, as discrepancies between docs and production often lead to gaps in security programs.
Undocumented APIs
Undocumented APIs are endpoints that exist in environments but are not officially recorded or tracked. They can be created by developers for testing, spun up quickly in microservices releases, or left over from legacy systems. These APIs do not appear in official catalogs, API specs, or monitoring dashboards.
Also called shadow APIs, these hidden endpoints operate outside normal governance. Because teams don’t know they exist, they rarely receive authentication, logging, or security reviews. Attackers actively hunt for them, knowing they are often weakly secured or completely open.
Undocumented APIs are a big reason why API discovery is so important for security. An API that isn’t recorded can’t be tested, patched, or controlled. Without discovery, these APIs quietly expand the API attack surface and add risk to security compliance, governance, and incident response.
Undocumented APIs bypass traditional checks, resulting in a lack of basic security features like proper authentication, rate limiting, or role-based access. This makes them prime targets for exploitation and data leakage.
Documented APIs Vs Undocumented
| Aspect | Documented APIs | Undocumented APIs |
|---|---|---|
| Visibility | Known to development and security teams | Hidden, often unknown to teams |
| Source | Created via Swagger, Postman, or RAML | Exist in code or runtime without a schema |
| Tracking & Maintenance | Included in API specs, actively maintained | Not tracked or officially maintained |
| Security Posture | Typically tested, authenticated, and monitored | Rarely tested, may lack authentication or logging |
| Governance | Follows standard release and approval processes | Bypasses governance and controls |
| Risk Level | Low (if documentation is managed and updated) | High (likely targets for "Shadow API" attacks). |
| Use Case | Intended for production or integration | Often legacy, temporary, or experimental endpoints |
| Example | An official public login endpoint. | A forgotten testing endpoint left in production. |
Risk of Incomplete API Discovery in Web Applications
Incomplete API discovery leaves gaps in how teams see and secure APIs. When some APIs are unknown or untracked, attackers find easy ways in. These blind spots increase risk and can affect data, compliance, and trust. Security teams must understand the dangers of missing API visibility.
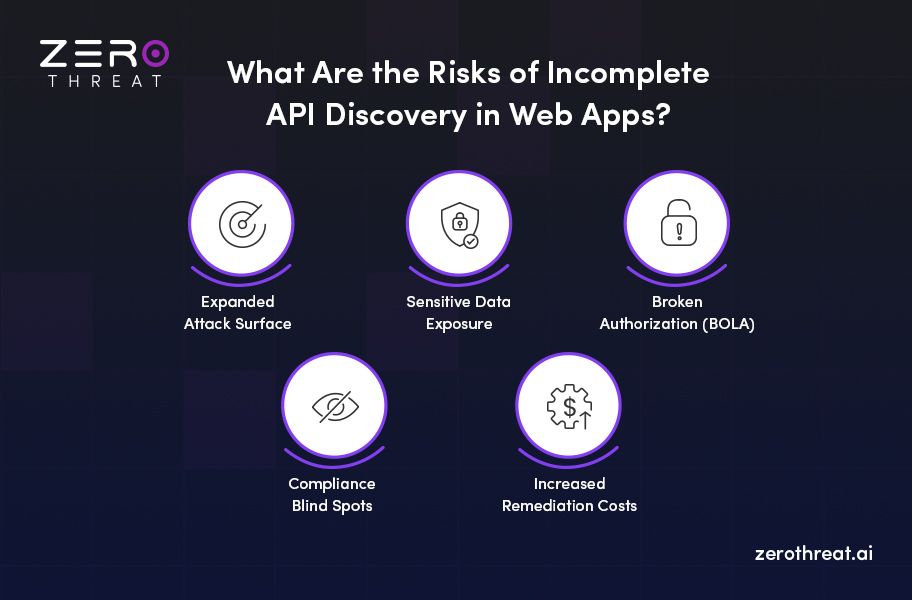
Expanded Attack Surface
Incomplete API discovery leaves Zombie and Shadow APIs exposed to the internet. These APIs bypass security controls and monitoring because they are not documented. Attackers actively scan for such hidden endpoints because they are easier to exploit and often lack authentication, rate limiting, or logging.
Sensitive Data Exposure
Undiscovered APIs may process personal, financial, or internal data without proper safeguards. Because security teams are unaware of them, encryption, access controls, and monitoring are often missing, increasing the risk of sensitive data exposure and unauthorized data access.
Broken Authorization (BOLA)
Hidden or undocumented APIs frequently skip proper authorization checks. This leads to Broken Object Level Authorization, where attackers can access or manipulate other users’ data by changing object identifiers. It is one of the OWASP Top 10 API security risks with a high damage impact if left unaddressed.
Compliance Blind Spots
APIs that are not documented or discovered cannot be governed or audited. This creates gaps in security compliance efforts for regulations like GDPR or PCI DSS. Security teams cannot prove data control when APIs handling sensitive data are missing from the API documentation.
Increased Remediation Costs
Finding a vulnerability after a breach is ten times more expensive than finding it during a scan. Incomplete discovery forces your team into a reactive mode. This wastes time, drains resources, and leads to costly downtime that could have been avoided with a shift-left security testing approach.
Discover and test exposed and undocumented APIs by simulating actual user interaction. Test API Security
Importance of Asset and API Discovery for Security
Maintaining a complete discovery of APIs and assets is the bare minimum to keep your web app secure. You cannot secure what you do not know exists, and in modern environments, what you don't see is exactly what attackers target. Discovery transforms this uncertainty into a structured, actionable roadmap for security risk reduction.
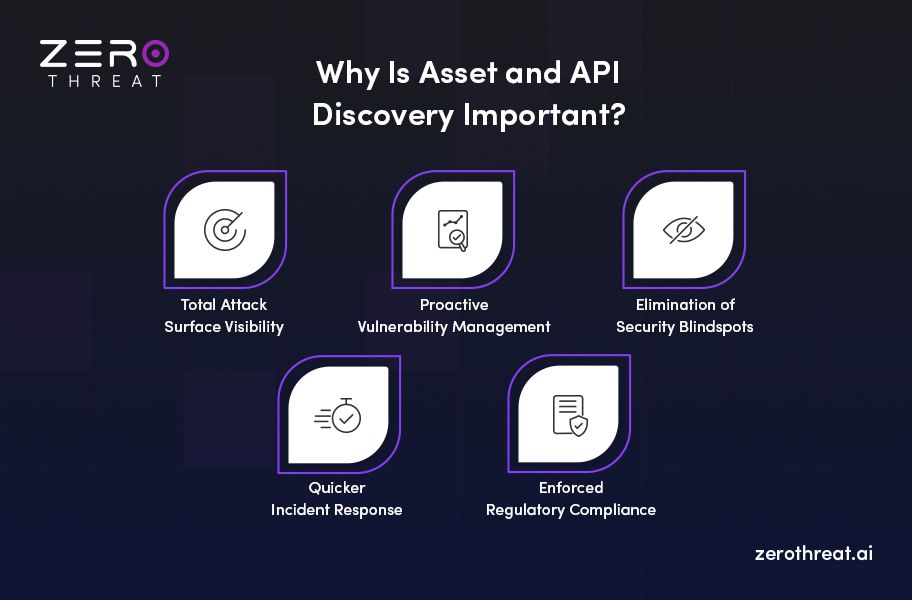
Total Attack Surface Visibility
Discovery uncovers the undocumented APIs by identifying every active endpoint and device across your network. This ensures that Shadow and Zombie APIs are brought under official management, leaving no unmonitored entry points for potential attackers to exploit.
Proactive Vulnerability Management
An accurate inventory allows you to map known vulnerabilities directly to your specific assets. By knowing exactly which versions and configurations are running, your team can prioritize patching and remediation efforts based on the real-world risk to your most critical systems.
Elimination of Security Blindspots
Continuous discovery prevents security misconfigurations where the actual state of your web apps and APIs deviates from your documentation. It flags new or modified assets in ensuring that security policies, like authentication and rate limiting, are applied immediately to every new endpoint.
Quicker Incident Response
During a breach, every second counts, and having a pre-mapped asset inventory is invaluable. It allows security teams to instantly identify compromised systems, understand their dependencies, and trace potential data leak paths. This reduces the time required to contain a live threat.
Enforced Regulatory Compliance
Most security frameworks, such as GDPR, HIPAA, and PCI DSS, mandate strict accounting of all systems handling sensitive data. Automated discovery provides the continuous, auditable record needed to prove compliance. It supports preventing the legal and financial penalties associated with unmanaged data flows.
How ZeroThreat Automates API Discovery
ZeroThreat automates API discovery by interacting with the web app like a real user and observing live behavior. It uncovers every reachable endpoint in your web app and APIs, which includes documented, hidden, and undocumented APIs. This process turns hidden risks into a clear, manageable inventory that protects your entire application.
- Dynamic Runtime Analysis: ZeroThreat identifies endpoints by interacting with your app in real-time while scanning. It doesn't need source code access, making it effective for uncovering APIs in any environment.
- Real User Simulation: The scanner mimics actual human behavior by clicking buttons and submitting forms. That allows ZeroThreat to trigger hidden API calls that static scanners and manual lists often miss.
- Comprehensive Application Crawling: It navigates every accessible route and page to map the full attack surface. This ensures even complex single-page applications (SPAs) are fully documented and secured.
- Deep Payload Mapping: ZeroThreat captures all client-server communication during scan sessions to understand parameter structures and request bodies. It creates a high-signal inventory that includes HTTP methods and expected responses.
- Continuous Asset Inventory: Discovered endpoints are automatically added to a centralized view in your Scan Report. With this, you can track changes and identify new "Shadow APIs" as they appear.
- Integrated Security Testing: Every discovered endpoint is automatically fed into ZeroThreat’s DAST tool for vulnerability testing. This ensures no API remains untested or exposed to potential threats.
API Discovery Best Practices for Security Teams
Finding APIs is only the first step; the real challenge is managing them effectively. Security teams need a proactive strategy to turn discovery into a repeatable, scalable process. Following these API best practices ensures that no hidden endpoint remains a threat to your organization.

Adopt Continuous Discovery
Static scans fail because environments change with each new update in APIs. Continuous discovery ensures you identify "Shadow APIs" the moment they go live, preventing unmanaged endpoints from becoming long-term backdoors into your production data.
Develop API Governance Policies
Security requires clear rules for API creation and deprecation. Strong governance ensures every new endpoint meets authentication standards and is registered in your central inventory. This eliminates the risk of "Zombie APIs," which is one of the key reasons behind attacks in legacy systems.
Go Beyond Documentation
Don't rely solely on the Swagger file, API documentation, or static analysis. Use dynamic tools such as ZeroThreat that mimic real user interactions by clicking buttons and submitting forms to uncover hidden runtime endpoints that logs might miss.
Maintain a Live Inventory
A central, real-time portal of all discovered assets is vital for incident response. It allows your team to see exactly what is exposed, including HTTP methods and payload structures, reducing the time, effort, and cost spent on discovering API endpoints that expose sensitive data.
Include Discovery into CI/CD
Integrating discovery directly into your build pipeline shifts security left. It automatically flags new or modified APIs during the SDLC, allowing you to fix vulnerabilities before they ever reach a public-facing environment.
Perform Regular Security Testing
API Discovery is the first step towards security; API testing is what allows you to know the exploitable vulnerabilities. Every discovered endpoint must be automatically fed into a DAST engine to validate exploits, ensuring that all reachable assets and APIs are secure.
Discuss securing your web apps and APIs at with ZeroThreat’s pentesting tool. Contact Us
Summing Up
Automated API and asset discovery are no longer optional for modern applications. APIs evolve constantly, and undocumented or hidden endpoints can expand the attack surface. Without continuous discovery, security teams are left with partial visibility and growing risk across the web application.
Shadow and zombie APIs create real security gaps when they remain undiscovered. Using manual inventory and static documentation cannot keep pace with rapid development and CI/CD changes. Security teams need continuous, runtime-based API discovery to identify real endpoints, reduce exposure, and stay secure.
ZeroThreat supports this by automating API and asset discovery through real application behavior with its API pentesting tool. It uncovers documented, hidden, shadow, and zombie APIs, then links discovery to security testing. This turns visibility into action and helps teams secure APIs at scale.
Frequently Asked Questions
Why do most security teams still miss APIs even after using API discovery tools?
Most tools rely on documentation or limited scans. They miss runtime-only, deprecated, or dynamically generated endpoints. As APIs change fast, point-in-time discovery quickly becomes outdated and creates blind spots.
How does automated API & asset discovery reduce API security blind spots?
What is the difference between automated API discovery and manual API inventory management?
How does ZeroThreat discover undocumented and shadow APIs?
Why is continuous API discovery critical for modern CI/CD environments?
Why is discovering undocumented APIs important for compliance and risk management?
Explore ZeroThreat
Automate security testing, save time, and avoid the pitfalls of manual work with ZeroThreat.


