
All Blogs
Why Business Logic Testing is the Next Frontier in Application Security

Quick Overview: Explore why business logic testing is the essential new priority in AppSec. Understand how logic flaws exploit working code and why traditional scanners consistently fail to detect them. This guide breaks down high-risk vulnerabilities like BOLA, compares manual and AI-powered testing approaches, and demonstrates how ZeroThreat’s agentic AI automates protection for unique workflows within modern CI/CD pipelines.
Imagine a vulnerability so simple that a six-character code could expose the travel details of millions, yet no security scanner could find it because, technically, the code worked perfectly. This was the reality of the 2019 Amadeus booking flaw that allowed hackers to access and modify their travel details and claim their frequent flyer miles without breaking a technical security rule.
This is the level of damage that business logic flaws can have if they are not detected, and the workflows are not fixed.
Every traditional automated testing tool and DAST scanners lack the context to understand human intent and often miss logic vulnerabilities that allow "working" code to be manipulated. That's one of the reasons why business logic testing is the new frontliner in AppSec.
In this blog, we’ll dive into the various approaches you can leverage to detect business logic vulnerabilities. We’ll cover which are the top logic flaws in web apps and how ZeroThreat’s AI-driven pentesting tool enables their detection.
Detect hidden logic flaws in minutes with ZeroThreat. Try for $0
ON THIS PAGE
- Why Business Logic Testing is the Next Frontier in AppSec
- Why Traditional Testing Tools Fail to Detect Logic Flaws?
- High-Risk Business Logic Vulnerabilities in Web Applications
- Different Approaches for Business Logic Testing
- Best Way to Detect Flaws in Business Logic: Hybrid Approach
- How ZeroThreat Enables Business Logic Security Testing
- Wrapping Up
Why Business Logic Testing is the Next Frontier in AppSec
Business logic testing is becoming the next frontier in application security because attackers no longer rely only on technical flaws. That means, attackers are identifying "working code" that behaves in unintended ways instead of simply finding a “broken code”. This is where a traditional security testing tool falls short of the need for context-aware security testing.
Attackers are Shifting Focus
As automated defenses against classic technical bugs improve, attackers are targeting what machines can’t easily test: business processes. These "silent" attacks don't trigger traditional alarms because the system appears to be functioning normally while data or funds are being stolen.
API-First Web Apps
APIs now handle roughly 71% of all web traffic and carry your most critical business logic. Since every API's workflow and sequence is unique, there are no universal "patterns" for scanners to follow, making specialized logic testing the only way to secure these digital experiences.
Speed of Modern Development
AI-accelerated development is pushing complex logic into production faster than ever before. Traditional manual penetration testing can’t keep up with the daily code releases, creating a gap that only continuous, automated business logic testing can fill.
Rise of Sophisticated Abuse
Logic-based vulnerabilities, like BOLA (Broken Object Level Authorization), consistently rank as top security risks because they are easy to exploit but nearly impossible to catch with standard tools. Testing the intent of a workflow is now also as critical as testing the syntax of the code.
Why Traditional Testing Tools Fail to Detect Logic Flaws?
Traditional security tools like DAST are built to identify broken code patterns and technical vulnerabilities. However, they lack the human context required to understand your specific business rules. Because logic flaws often involve legitimate requests used in the wrong order or context, automated scanners simply see them as normal, authorized traffic.
- Inability to Detect Anomalies: Tools treat all inputs literally; they can't recognize when a technically valid request is actually a malicious exploit.
- Absence of Business Context: Scanners identify technical bugs but fail to understand specific business rules, leaving your application's unique logic and workflows unvalidated.
- Lack of Standardized Patterns: Unlike SQL injection, logic flaws don't have predictable patterns, making it nearly impossible for automated tools to spot them.
- Multi-Step Workflow Blindness: Traditional tools usually test isolated endpoints and struggle to understand the complex relationships between sequential, multi-step API calls.
- Focus on Syntax Over Intent: Automation check for malicious characters like <script> rather than testing code that can be used in ways the business never intended.
High-Risk Business Logic Vulnerabilities in Web Applications
Here is a breakdown of business logic vulnerabilities categorized by the specific functional areas they impact. These categories highlight how attackers exploit the business logic rules of your application.
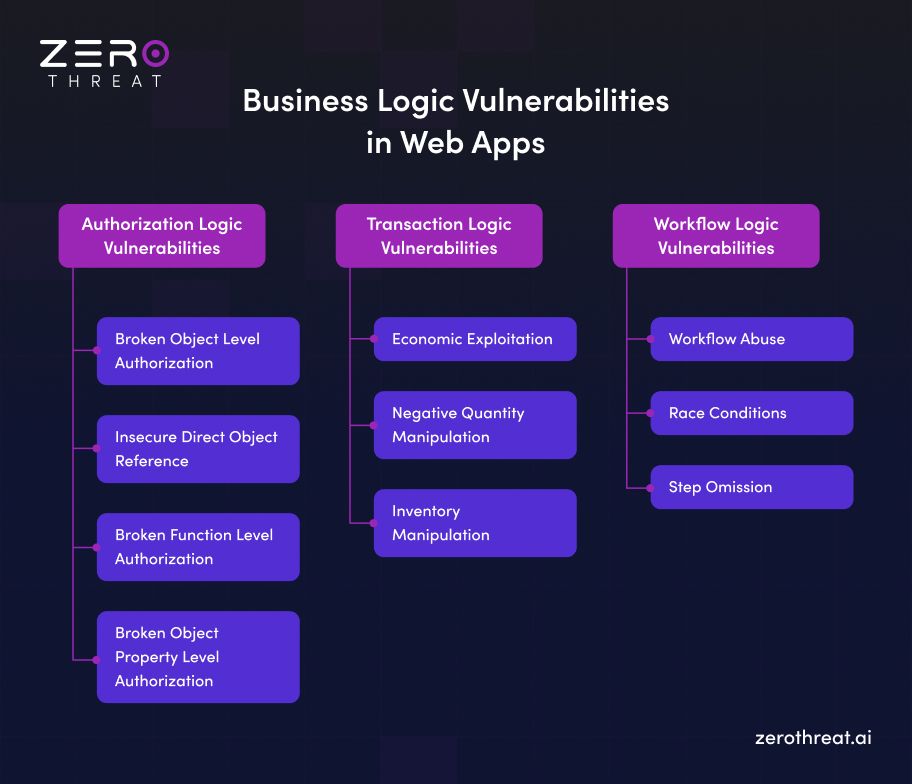
Authorization Logic Vulnerabilities
These vulnerabilities focus on how an application verifies identity and controls what data a user can see or modify.
Broken Object Level Authorization: BOLA is one of the most critical API risks. It happens when a system fails to check if a user should have access to a specific resource. For example, an attacker might harvest medical records or vehicle information by simply changing a ID number in a web address.
Insecure Direct Object Reference: IDOR is similar to BOLA; attackers exploit predictable ID patterns to access unauthorized data. If IDs are sequential, a script can easily iterate through them to steal information from other users.
Broken Function Level Authorization: BFLA flaw allows a regular user to access administrative or "hidden" functions. A common example is a standard user deleting other accounts by directly calling an admin endpoint that lacks proper permission checks.
Broken Object Property Level Authorization: Here, a user is allowed to see a piece of data, but can also access hidden sensitive properties. An example of BOPLA is a social media API returning private phone numbers or IP addresses that should not be visible to the public.
Transaction Logic Vulnerabilities
These flaws target the financial rules of a business, often leading to direct revenue loss or fraud.
Economic Exploitation: Attackers play the system by stacking discount codes that shouldn't work together or manipulating pricing logic to get items for free.
Negative Quantity Manipulation: This classic logic flaw involves entering a negative number in an order field. A traditional scanner might see it as a valid number, but the business logic might accidentally issue a credit to the user's account instead of charging them.
Inventory Manipulation: Malicious actors use bots to automate purchase flows much faster than humans. This allows them to monopolize ticket sales or limited product launches, preventing legitimate customers from buying.
Workflow Logic Vulnerabilities
This category involves manipulating the specific order of steps required to complete a business process.
Workflow Abuse: Attackers bypass mandatory steps in a process. A dangerous example is triggering a product delivery system before the payment verification step has actually been completed.
Race Conditions: These occur when a system uses shared data at the same time. By sending multiple requests in a split second, an attacker might be able to redeem a single gift card multiple times before the system can update the balance.
Step Omission: Users bypass registration or verification hurdles by moving directly to the final "order generated" or "booking successful" URL in a multi-step sequence.
Secure your critical API workflows against high-risk logic abuse. Assess Logic Risks
Different Approaches for Business Logic Testing
Testing business logic requires a deep understanding of human intent and unique application workflows. Here are some of the approaches that security teams and developers leverage to detect business logic flaws.
Manual Penetration Testing
Manual penetration testing remains the core standard for identifying complex logic flaws because humans can understand context and intent in ways machines cannot. A skilled tester can think like an attacker to find ways in which workflows can be manipulated for malicious gain. They are uniquely capable of performing deep-dives into your business model to uncover risks that require creative, multi-step thinking.
- Contextual Reasoning: Humans can identify when a technically valid request, like a 90% discount, is actually a logic failure.
- Creative Chaining: Testers can link multiple minor issues together to create a significant exploit that automated tools would overlook.
- Domain Expertise: Experts understand the specific nuances of your industry, such as how a healthcare portal must handle patient data differently than a retail site.
Limitation: While highly effective, manual testing is often expensive and difficult to scale for companies deploying code daily. Because it typically happens late in the development cycle, it functions as a one-time test rather than a continuous safety net.
AI-Powered and Agentic Testing
The rise of AI-powered security tools is transforming how we approach business logic at scale. These tools use machine learning and autonomous "AI agents" to simulate real-world attacker behavior and explore complex application paths. Unlike traditional scanners, agentic AI can reason through a system, adapting its workflow to uncover logic abuse and validating whether a vulnerability is actually exploitable.
- Adaptive Workflows: Controlled AI agents can explore non-linear user journeys to find hidden gaps in application logic.
- Anomaly Detection: AI excels at flagging unusual API behavior or suspicious data structures that might indicate a zero-day exploit.
- Automated Validation: Agentic systems can prove an exploit exists by providing evidence-driven reports, reducing the manual effort required for verification.
Limitation: AI is not a complete replacement for human judgment yet. While it can detect symptoms of an attack, it can still struggle to fully grasp whether a specific 90% discount is a legitimate marketing feature or a logic error.
Developer-Integrated Testing
The developer-integrated testing approach is based on the idea of "shifting context left," by putting security into the hands of developers. By integrating security validation directly into the CI/CD pipeline, organizations can catch logic flaws during the development phase rather than after deployment. This methodology transforms security from a final test process into a continuous practice that gets adapted alongside the code.
- CI/CD Integration: Automated scans and custom scripts run every time code is committed, ensuring continuous protection.
- Security Unit Tests: Developers write specific tests to validate that authorization logic and business rules work correctly across different user contexts.
- API Contract Testing: These tests ensure that your APIs behave exactly as intended, preventing unauthorized access or data leakage early in the lifecycle.
Limitation: It’s difficult to ensure these tests stay updated as the business logic evolves rapidly. And once the application scales, maintaining a complete understanding of business logic can be complex for developers.
Best Way to Detect Flaws in Business Logic: Hybrid Approach
Each method has its own limitations: manual testing is too slow to scale; AI can sometimes lack full business context, and developer-only testing might miss creative ways an attacker would manipulate the system. Therefore, using a hybrid approach for business logic testing is the ideal way to ensure complete coverage without slowing down your releases.
By combining automated technical scanning with agentic AI and human expertise, you build a resilient defense. Here is how you can leverage the hybrid approach:
- Establish a Technical Baseline: Use automated testing tools to quickly detect OWASP Top 10 and CEW Top 25 vulnerabilities.
- Map Critical Workflows: Identify your top five high-risk APIs and write custom automated test scripts to validate their unique business rules.
- Automate High-Signal Tests: Integrate custom scripts and AI validation into your CI/CD pipeline to catch recurring logic errors automatically.
- Schedule Periodic Manual Tests: Complement your daily automation with quarterly manual penetration tests to uncover complex, multi-step logic vulnerabilities.
- Continuous Feedback Loop: Use clear reports to provide developers with the evidence they need to fix logic flaws during the build.
Test complex workflows with ZeroThreat’s AI-powered pentesting. See It in Action
How ZeroThreat Enables Business Logic Security Testing
ZeroThreat redefines the next frontier of AppSec by combining automated pentesting with agentic AI security testing. It can simulate real-world attacker behavior to find exactly where your business rules can be manipulated.
- Agentic AI Pentesting: ZeroThreat utilizes controlled, AI-powered reasoning that adapts to complex user journeys, uncovering logic abuse by exploring non-linear attack paths just like a human attacker would.
- Behavioral Anomaly Detection: The tool leverages an AI to analyze anomalous behavior in real-world apps, helping to catch zero-day vulnerabilities and unique logic flaws that don't fit standard templates.
- Seamless CI/CD Integration: It is purpose-built for DevSecOps, automating business logic scans on every build to catch flaws before they reach production while connecting with issue tracking tools like Jira, GitHub Issues, and Trello.
- Contextual Remediation: Every finding includes AI-driven remediation reports with request/response evidence and specific code examples to help developers fix logic flaws 10x faster.
Wrapping Up
Securing an application is no longer just about patching broken code. Today’s attackers exploit business logic, the actual rules and workflows of your app. Because traditional scanners lack the context to understand your unique processes, these silent vulnerabilities often go undetected until it’s too late.
To protect your platform, keep these essentials in mind:
- Understand Context: Logic flaws live in code that technically "works" but behaves incorrectly from a business perspective.
- Test Critical Paths: Prioritize testing sensitive areas like payments, refunds, and account access.
- Use Smart Automation: Manual testing provides deep insight, but cannot match the speed of daily deployment cycles.
Modern security requires a tool that understands your application's intent. ZeroThreat fills this gap by using agentic AI to automate business logic testing with 98.9% accuracy. By integrating directly into your development pipeline, it catches complex vulnerabilities early, allowing you to ensure security with every release.
Frequently Asked Questions
How is business logic testing different from traditional application security testing?
Business logic testing focuses on how workflows, roles, and business rules behave under real-world abuse. On the other hand, traditional application security testing looks for technical flaws like injection or XSS. Logic testing evaluates intent, sequence enforcement, and transaction integrity rather than just code-level weaknesses.
Why do SAST and DAST tools fail to detect business logic vulnerabilities?
When should business logic testing be integrated into the SDLC?
What industries are most at risk of business logic vulnerabilities?
Are business logic vulnerabilities related to broken access control?
Explore ZeroThreat
Automate security testing, save time, and avoid the pitfalls of manual work with ZeroThreat.


