All Blogs
Shift-Left vs Shift-Right: Why Modern Teams Need a Continuous-Testing Middle Layer

Quick Overview: This blog explores why shift-left and shift-right testing alone are no longer sufficient for modern software teams. It explains the growing need for a continuous-testing middle layer that validates real-world risk, reduces late-stage surprises, and helps businesses ship faster with confidence and control.
For more than a decade, software engineers have debated where testing should happen. The industry responded with two powerful movements: Shift-Left, which pushed testing earlier into development. And another is Shift-Right, which emphasizes monitoring and validation in production. Both approaches promised speed, quality, and resilience, and both delivered measurable value.
Yet in today’s reality of cloud-native architectures, microservices, continuous delivery, AI-driven systems, and relentless release cycles, something is fundamentally broken.
Despite adopting shift-left testing practices, teams still ship vulnerabilities. Despite heavy investment in shift-right observability, failures still reach customers. Security incidents are detected faster, but still too late. Quality issues are observed, but only after reputational damage.
The uncomfortable truth is this: Shift-Left and Shift-Right were never designed to work alone.
Modern software delivery has created a vast blind spot between code commit and real-world usage. And that’s a middle layer where most risks emerge, but the least testing happens. This gap is where integrations fail; configurations drift, APIs break, and security assumptions collapse.
To compete at scale, modern organizations must move beyond a binary testing mindset and adopt a continuous testing middle layer. This layer should validate quality, security, and performance throughout the software lifecycle, including continuous web app security testing across applications and APIs.
In this shift-left vs shift-right testing article, we will discuss why the middle layer is becoming essential and how it delivers measurable business value.
Start securing what attackers look for—before your next release. Sign Up Free
On This Page
- What is Shift Left Testing?
- Core Objectives of Shift Left Testing
- Benefits of Shift-Left Testing
- Limitations of Shift-Left in Modern Environments
- Types of Shift-Left Testing
- What is Shift-Right Testing?
- Core Objectives of Shift-Right Testing
- Benefits of Shift-Right Testing
- Limitations of Shift-Right for Risk Management
- Types of Shift-Right Testing
- What is a Continuous-Testing Middle Layer?
- Why Business Leaders Should Care About Continuous Testing?
- Shift-Left vs Shift-Right vs Continuous-Testing
- Benefits of Continuous Testing: Combining Shift-Left and Shift-Right Testing
- How to Implement Shift-Left and Shift-Right Testing Together with ZeroThreat?
- Conclusion
What is Shift Left Testing?
Shift-left testing focuses on moving testing activities earlier in the software development lifecycle (SDLC). The primary objective of the shift-left approach is to identify defects, vulnerabilities, and design flaws before code reaches production, when fixes are cheaper and faster.
For example, shifting left on performance testing allows teams to identify and fix performance issues early in the development phase, instead of discovering them after deployment. By addressing bottlenecks at the source, developers can prevent costly problems, such as a web application crashing when real-world user traffic suddenly increases.
The term “shift left” comes from the traditional left-to-right view of the software development lifecycle (SDLC), where design and development appear at the beginning, and deployment comes at the end.
Shifting left means moving testing activities earlier in this timeline, embedding them into development rather than postponing them until production.
When implementing shift-left testing, teams should focus on the following priorities:
- Gaining a deep understanding of application performance goals, business requirements, and user expectations.
- Building strong unit, integration, and functional test coverage early in development.
- Automating end-to-end testing workflows to ensure consistency and speed.
- Adopting test-driven development (TDD) and behavior-driven development (BDD) practices to improve quality from the start.
Core Objectives of Shift Left Testing
Shift-left testing strategy focuses on catching issues early, embedding quality into development, reducing late-stage testing risks, and enabling faster, more reliable software releases through continuous validation.
Detect Defects Earlier
Shift-left testing moves validation activities into the earliest stages of development, where defects are easier and less expensive to fix. Identifying issues during coding or integration prevents them from becoming deeply embedded in the system. Early detection reduces rework, limits cascading failures, and avoids costly fixes that would otherwise occur during late-stage testing or after release.
Improve Developer Accountability for Quality
By integrating testing directly into the development workflow, shift-left practices make quality a shared responsibility rather than a downstream concern. Developers receive immediate feedback on their code through unit tests, automated checks, and CI pipelines. This encourages ownership of quality, reduces reliance on QA, and leads to more stable, maintainable software over time.
Reduce Downstream Testing Bottlenecks
Traditional testing approaches often create bottlenecks late in the release cycle when defects accumulate, and testing windows shrink. Shift left methodology spreads validation across the development lifecycle, reducing the volume of issues discovered at the end. This balances workloads between teams, minimizes last-minute fixes, and prevents release delays caused by overloaded QA and testing teams.
Shorten Release Cycles
Shift-left testing in DevOps enables faster and more predictable releases by eliminating late-stage surprises. Continuous testing and early feedback allow teams to validate functionality incrementally as features are built.
With fewer defects reaching staging or production, releases require less rework and stabilization time, allowing organizations to ship updates more frequently and respond faster to market or customer needs.
Benefits of Shift-Left Testing
Over the past decade, engineering organizations have increasingly adopted shift-left testing as a core development practice. By embedding testing earlier in the software development lifecycle, teams gain several tangible technical and operational benefits:
- Improved Software Quality: Continuous testing and rapid feedback help identify defects early, preventing small issues from escalating into system-wide failures later in the lifecycle.
- Faster Time-to-Market: Resolving defects during development reduces late-stage rework, allowing teams to ship features and updates more quickly and with greater confidence.
- Higher Developer Productivity: Early feedback enables developers to fix issues while the code context is still fresh, minimizing costly context switching and improving overall efficiency.
- Reduced Cost of Fixes: The cost of fixing defects increases significantly the later they are discovered. Addressing issues during coding or integration is far more cost-effective than remediation in production.
- Better Collaboration Between Teams: Shift-left testing encourages closer alignment between development, QA, and DevOps, reducing handoff friction and fostering shared ownership of quality.
- More Reliable Releases: With fewer defects reaching production, releases become more stable, reducing the risk of outages, rollbacks, and emergency patches.
Limitations of Shift-Left in Modern Environments
However, shift-left testing approach has structural blind spots that business leaders often underestimate:
- Incomplete Context: Early tests operate on partial systems, mocks, or assumptions.
- Low signal-to-Noise Ratio: Many findings are theoretical and not exploitable.
- Limited Business Logic Coverage: Complex authorization paths and workflow abuse rarely surface during unit or static testing.
- Developer Fatigue: Excessive findings reduce trust in security tools.
New risks appear daily. Continuous pentesting keeps you ahead. Start Continuous Pentesting
Types of Shift-Left Testing
Organizations face security risks throughout the build, deployment, and runtime phases of the software lifecycle. Adopting a DevSecOps approach with shift-left testing introduces developer-friendly metrics early in the process. This helps you reduce human error during build and deploy stages while strengthening workload protection in production environments.
Common techniques used in shift-left testing include:
- Static Application Security Testing (SAST): Examines source code, bytecode, or binaries to identify security vulnerabilities early in development.
- Dynamic Application Security Testing (DAST): Uses black-box testing to detect security weaknesses by scanning a running application.
- Threat Modeling: Evaluates design decisions and system components to anticipate potential security risks now and in the future.
- Security Architecture Reviews: Assess system designs to identify, evaluate, and mitigate risks from both current and emerging threats.
- Container Image Scanning: Analyzes container layers to detect known vulnerabilities, misconfigurations, and malicious components.
- Code Signing: Applies digital signatures to software artifacts to verify authenticity and integrity before execution.
- Continuous Performance Testing (CPT): Continuously evaluates system performance throughout development to detect bottlenecks and scalability issues early.
What is Shift-Right Testing?
Shift-right focuses on observing and validating applications after deployment, using runtime monitoring, logging, threat detection, and incident response mechanisms.
Shift-right testing extends quality validation beyond deployment and into production, where real users interact with live systems under real-world conditions. Instead of ending at release, testing continues in production by observing actual usage patterns, system performance, and user behavior.
While shift-left testing focuses on detecting defects early during design and development, shift-right testing validates how the application behaves in real-life scenarios. It helps ensure the software performs reliably in production, meets user expectations, and continues to adapt as requirements and usage evolve.
Core Objectives of Shift-Right Testing
Shift-right testing focuses on validating security, performance, and reliability in production by observing real user behavior, real traffic, and real threats.
Detect Real-World Attacks
Shift-right practices enable organizations to detect attacks as they occur in live production environments. Unlike pre-release testing, production monitoring exposes real threat behavior, including misuse, abuse patterns, and emerging attack techniques.
Observing actual attacker activity helps security and operations teams validate defenses, uncover blind spots, and adapt controls based on real-world threats rather than theoretical models.
Understand User Behavior at Scale
By analyzing production telemetry, logs, and user interactions, shift-right approaches provide visibility into how real users behave at scale. This insight helps teams distinguish between normal and abnormal activity, identify friction points, and detect suspicious behavior that may indicate abuse or compromise.
Understanding real usage patterns allows organizations to optimize performance, improve security controls, and make data-driven decisions.
Respond to Incidents Quickly
Shift-right strategy enables faster incident detection and response by continuously monitoring production systems for anomalies, failures, or security events.
Real-time alerts, observability, and automated responses reduce mean time to detect and contain incidents. This rapid response capability limits damage, minimizes downtime, and helps teams remediate issues before they escalate into widespread outages or breaches.
Measure Actual Operational Risk
Shift-right testing provides measurable insight into operational risk by observing how systems perform under real conditions. Teams can assess exposure based on real traffic, real users, and real attacks rather than assumptions.
As a result, this allows organizations to quantify risk more accurately, prioritize remediation efforts, and align security and reliability investments with actual business impact.
Benefits of Shift-Right Testing
Shift-right testing strategy extends validation into production, allowing teams to learn from real-world usage and continuously improve system reliability, security, and user experience.
- Higher Confidence in Production Releases: Testing in live environments provides accurate insight into how applications perform under real traffic and workloads. This helps teams validate stability, usability, and reliability with greater confidence after deployment.
- Improved User-Centric Development: Real user behavior and feedback reveal how features are actually used, enabling teams to refine user journeys, improve experience, and align development with real customer needs.
- Enhanced System Resilience: Monitoring and learning from live failures allows organizations to proactively address weaknesses, resulting in more fault-tolerant and resilient systems over time.
- Faster Incident Detection and Recovery: Continuous production monitoring enables teams to identify issues quickly, reduce mean time to detect and resolve incidents, and minimize downtime.
- Data-Driven Optimization: Observability metrics and real-world performance data help teams prioritize improvements based on actual impact rather than assumptions.
- Better Risk Visibility: Shift-right testing exposes real operational and security risks, helping teams understand true production exposure and make informed decisions.
Security gaps are costly. Predictable pricing isn’t. View Pricing
Limitations of Shift-Right for Risk Management
Despite its strengths, shift-right has critical drawbacks:
- Issues are discovered after exposure
- Incident response is expensive and disruptive
- Customer trust may already be impacted
- Regulatory consequences may already apply
Types of Shift-Right Testing
To implement shift-right testing, development teams run controlled experiments in production or near-production environments toward the later stages of the software lifecycle. The goal is to evaluate real-world functionality, performance, resilience, failure tolerance, and user experience under live conditions.
Common shift-right testing techniques that enable real-time visibility and operational control include:
- Security Information and Event Management (SIEM): Centralizes logs and security data to detect, analyze, and respond to threats in production.
- Security Orchestration, Automation, and Response (SOAR): Automates and coordinates incident response workflows across tools and teams, reducing manual effort.
- Canary Deployments: Releases new functionality to a small group of users first, allowing teams to validate changes before a full rollout.
- Deployment Rings: Gradually deploys updates across controlled user groups to limit blast radius and monitor impact.
- A/B Testing: Compares multiple versions of a feature or experience by measuring real user responses against defined success metrics.
- Fault Injection Testing: Deliberately introduces failures to evaluate system behavior and recovery under adverse conditions.
- API Security Testing: Analyzes service-to-service communication to detect abnormal behavior and security incidents.
- Chaos Engineering: Intentionally disrupts systems to test resilience and uncover weaknesses before real failures occur.
- Blue-Green Deployments: Runs two production environments in parallel and gradually shifts traffic to the new version, enabling fast rollback if issues arise.
What is a Continuous-Testing Middle Layer?
A continuous-testing middle layer is a persistent validation capability that operates between shift-left and shift-right testing.
It continuously tests applications and APIs in environments that closely resemble production, without waiting for incidents and without relying on incomplete early assumptions.
Why Business Leaders Should Care About the Continuous Testing
Reduces the Cost Curve of Risk
Security cost increases exponentially the later an issue is discovered. Middle-layer testing finds exploitable issues before public exposure, but after systems are realistic-delivering optimal cost efficiency.
Improves Release Confidence
Executives care about predictability. Continuous middle-layer testing reduces last-minute release delays caused by late-breaking security findings.
Protects Revenue and Brand Trust
Many data breaches stem from authorization flaws, business logic abuse, or exposed APIs—issues rarely caught early but often exploited quickly. Middle-layer validation directly targets these risks.
Aligns Security with Delivery Speed
Instead of forcing teams to slow down, the middle layer enables secure velocity by validating continuously in the background.
Shift-Left vs Shift-Right vs Continuous-Testing
| Key Factors | Shift-Left Testing | Shift-Right Testing | Continuous-Testing Middle Layer |
|---|---|---|---|
| Primary Objective | Prevent defects early in development | Detect and respond to issues in production | Validate real-world risk before exposure |
| SDLC Stage | Design, coding, CI/CD | Post-deployment, runtime | Pre-prod, staging, live-like environments |
| Testing Context | Partial systems, mocked services | Live production traffic | Realistic configurations and integrations |
| Risk Detection Timing | Early but theoretical | Late but real | Early enough and realistic |
| Type of Findings | Code issues, misconfigurations, known patterns | Active attacks, anomalies | Exploitable vulnerabilities and logic abuse |
| Business Logic Coverage | Limited | Reactive only | Strong, workflow-aware validation |
| API Security Effectiveness | Low to moderate | Moderate (detection-based) | High (authenticated, behavior-driven) |
| False Positives | High | Low | Very low (validated findings) |
| Remediation Cost | Lowest per issue | Highest per incident | Optimized cost-to-fix |
| Impact on Release Velocity | Can slow developers if noisy | No impact on release speed | Improves confidence without slowing delivery |
| Ownership | Developers | Security Operations / SOC | Shared: AppSec, DevOps, Product |
| Feedback Loop Speed | Fast but incomplete | Slow and post-impact | Continuous and actionable |
| Customer Trust Impact | Indirect | After damage occurs | Preventive and trust-preserving |
| Compliance Readiness | Partial | Reactive evidence | Continuous and audit-friendly |
| Business Value | Cost avoidance in early stages | Incident containment | Risk reduction with delivery assurance |
| Strategic Limitation | Lacks real-world context | Too late to prevent damage | Requires mature security alignment |
Every application environment is different. Let’s secure yours. Talk to an Expert
Benefits of Continuous Testing: Combining Shift-Left and Shift-Right Testing
Engineering organizations that adopt both shift-left and shift-right testing approaches can expect the following benefits:
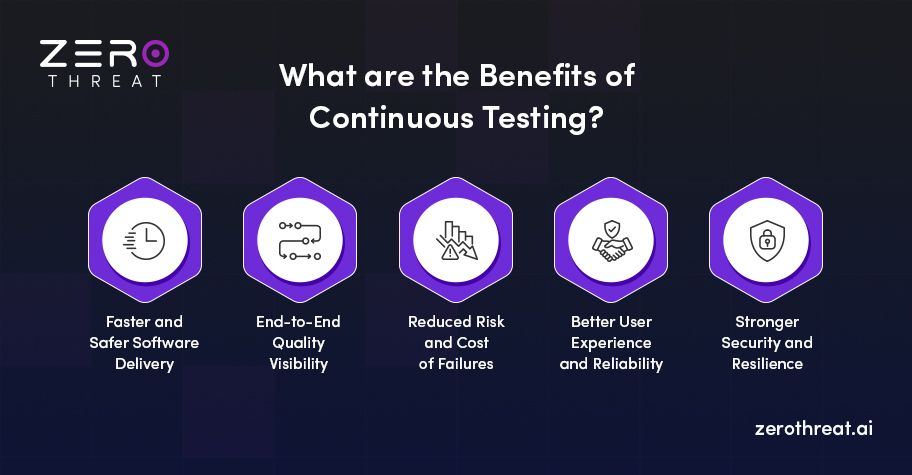
Faster and Safer Software Delivery
By testing early and validating continuously in production, teams detect issues before release and confirm stability after deployment. This reduces late-stage surprises, accelerates delivery, and ensures new features reach users quickly without compromising reliability or quality.
End-to-End Quality Visibility
Combining shift-left and shift-right testing provides full lifecycle visibility, from code creation to real-world usage. Teams gain insight into how early design decisions affect production behavior, enabling continuous improvement, and more informed engineering decisions.
Reduced Risk and Cost of Failures
Early testing prevents defects from reaching production, while production monitoring catches real-world issues quickly. This dual approach minimizes the financial, operational, and reputational impact of failures by shortening detection and recovery times.
Better User Experience and Reliability
Shift-left ensures features are built correctly, while shift-right validates how users actually experience them. Together, they help teams optimize performance, usability, and stability based on real usage patterns and feedback.
Stronger Security and Resilience
Security checks during development reduce vulnerabilities, while production monitoring detects live attacks and abuse. Continuous testing across both phases strengthens defenses, improves resilience, and enables faster response to emerging threats.
How to Implement Shift-Left and Shift-Right Testing Together with ZeroThreat?
A continuous testing approach requires validating security, behavior, and risk across the entire lifecycle, not just during development or after deployment.
ZeroThreat enables this by focusing on the human layer, which is involved in the majority of real-world security failures.
Embed Prevention Early (Shift Left)
Integrate ZeroThreat early in the development and deployment process to identify risky human behaviors, insecure workflows, and potential social engineering exposure. This helps teams reduce human error before applications reach production.
Monitor Real Behavior in Production (Shift Right)
Once systems are live, ZeroThreat continuously observes real user behavior to detect phishing attempts, impersonation, abnormal access, and insider risk indicators. This validates whether early assumptions hold true under real-world conditions.
Create a Continuous Feedback Loop
Insights from live environments are fed back into training, controls, and development practices. This allows teams to continuously improve security posture based on actual threats rather than theoretical risks.
Automate Risk Reduction
ZeroThreat supports automation by triggering alerts, workflows, and corrective actions when risky behavior is detected, reducing response time and limiting impact.
Measure and Optimize Over Time
By tracking behavioral risk trends and attack outcomes, organizations can measure effectiveness, prioritize improvements, and continuously strengthen resilience.
Together, this approach ensures continuous validation, faster response, and reduced human-driven risk across the entire software and security lifecycle. Sign up for free and implement continuous testing with ZeroThreat.
Don’t wait for a breach! Sign up and start pentesting your application today. Try for FREE
Conclusion: Moving Beyond “Left vs Right” to Continuous Confidence
The shift-left vs shift-right testing debate reflects how software delivery used to work—linear, predictable, and slower. Modern digital businesses no longer operate in that reality.
Shift-left testing remains essential for building secure foundations and reducing early defects. Shift-right practices are critical for resilience and incident response in production. However, on their own, neither approach provides the continuous assurance business leaders require to release faster without increasing risk.
This is why a continuous-testing middle layer is no longer optional. It bridges development intent with operational reality by validating exploitable risk in realistic environments, before customers, attackers, or regulators discover it.
For modern teams, security is not about choosing where to test. It is about testing continuously, where risk actually exists. Organizations that adopt this middle layer gain predictable releases, lower remediation costs, stronger compliance posture, and sustained customer trust.
Frequently Asked Questions
What is Shift Left testing?
Shift Left testing is the practice of moving testing and security checks earlier in the software development lifecycle. It helps teams identify defects and vulnerabilities during design and development, reducing rework, lowering remediation costs, and improving code quality before applications reach production.
What is Shift Right testing?
What is the difference between Shift Left and Shift Right?
Why do teams need continuous testing?
Can you combine Shift Left and Shift Right?
Is Shift Left testing enough on its own?
What testing belongs to Shift Right?
How does continuous testing work in DevOps?
When should teams use Shift Right testing?
How to implement a continuous testing approach?
Explore ZeroThreat
Automate security testing, save time, and avoid the pitfalls of manual work with ZeroThreat.