All Blogs
Modern XSS Filter Bypass: Techniques and Defense Strategies

Quick Overview: Modern web security requires moving beyond basic filters to stop sophisticated cross-site scripting attacks. Explore advanced bypass techniques like mutation XSS and polyglot payloads that frequently evade traditional scanners. Learn practical prevention strategies like context-aware encoding and discover how ZeroThreat’s AI-powered automated pentesting detects vulnerabilities with 98.9 percent accuracy to secure your applications effectively.
The advanced XSS attacks are evolving faster than most defenses can keep up. In fact, recent reports show that cross-site scripting vulnerabilities continue to appear in a significant share of newly disclosed CVEs, with multiple high-severity cases reported in a single week in 2026.
Even more concerning, advanced research shows that up to 80% of sophisticated XSS payloads can bypass traditional WAF protections when obfuscation and mutation techniques are used. This highlights a clear gap between detection logic and real browser execution.
Modern applications rely heavily on client-side rendering, APIs, and dynamic JavaScript. This expands the attack surface and makes filter-based defenses unreliable. Attackers no longer depend on basic payloads. They use encoding, DOM manipulation, and AI-assisted payload generation to bypass filters that were once considered effective.
This guide breaks down how these modern XSS attacks work, why filters fail, and what strategies you can use to detect them, and how ZeroThreat’s AI-driven automated penetration testing enables you to detect and fix vulnerabilities before the attack impacts real users.
Detect and stop modern XSS bypasses with ZeroThreat’s AI-powered automated pentesting. Start For FREE
ON THIS PAGE
- What is XSS Filter Bypass?
- Why Modern XSS Attacks Still Bypass Filters
- Three Types of XSS Attacks (With Difference Table)
- Reflected vs. Stored vs. DOM
- Modern XSS Filter Bypass Techniques
- How Attackers Bypass Cross-Site Scripting Filters
- Examples of XSS Filter Bypasses
- How to Prevent XSS Attack Bypasses (Effective Strategies)
- How ZeroThreat Simplifies XSS Vulnerability Detection and Fixing
- Conclusion: What to Do Next
What is XSS Filter Bypass?
An cross-site scripting (XSS) filter bypass is a strategic method used by attackers to avoid security protections designed to stop cross-site scripting. These mechanisms typically scan user input to detect and remove suspicious code patterns. Attackers use these techniques to slip malicious payloads past web application firewalls.
Evasion techniques often exploit how browsers interpret malformed HTML or specific character encodings. By using methods like hexadecimal or Base64 encoding, attackers disguise their intent from simple string matching filters. This allows malicious JavaScript to execute even when active filters are present.
Relying on filtering is not a foolproof defense because hundreds of different bypass methods exist. Security experts note that filters often struggle with complex stored or DOM based attacks. Authentic protection requires a layered approach beyond basic input validation and pattern matching.
Why Modern XSS Attacks Still Bypass Filters
Modern XSS attacks bypass filters because web applications rely on pattern-based defenses, while browsers and JavaScript engines interpret input in flexible ways that attackers can manipulate.
Here are the limitations of XSS filtering that allow attackers to bypass through them:
Pattern-Based Filtering Cannot Cover All Variations
Most XSS filters rely on signatures like <script> or known payload patterns. Attackers easily bypass these checks by modifying syntax, encoding inputs, or using alternate execution methods. This creates gaps where malicious code passes through without detection.
Browsers Automatically Fix and Execute Malformed Code
Modern browsers are designed to correct broken HTML and JavaScript so pages still render properly. Attackers exploit this behavior by crafting malformed inputs that filters miss, but browsers reconstruct and execute as valid scripts.
Multiple Execution Paths Beyond Script Tags
Filters often focus on blocking <script> tags, but attackers use event handlers, SVG tags, or inline attributes to execute code. These alternative vectors allow JavaScript execution without triggering traditional filter rules.
Encoding and Obfuscation Hide Malicious Payloads
Attackers use encoding techniques like URL encoding or Base64 to disguise payloads. Many filters fail to decode input before analysis, while browsers automatically decode and execute it, allowing hidden scripts to run successfully.
Client-Side and DOM-Based XSS Are Hard to Detect
Modern applications rely heavily on client-side rendering. DOM-based cross-site scripting happens entirely in the browser, which means server-side filters and WAFs cannot see or block the attack during request processing.
Rapid Evolution of XSS Bypass Techniques
Attackers continuously develop new payload variations and bypass strategies. Research shows that even advanced defenses like WAFs struggle to detect highly obfuscated attacks, making filtering alone an incomplete security approach.
3 Types of XSS Attacks (With Difference Table)
Modern cross-site scripting vulnerabilities fall into three primary categories based on how the malicious payload reaches the victim. Understanding these specific types helps developers implement targeted security controls and validation strategies effectively.
Reflected XSS
Reflected XSS occurs when a script is immediately reflected off a web application into the user's browser. It often spreads through malicious links in emails or search results. When a victim clicks the link, the script executes instantly within their session.
Stored XSS
Stored cross-site scripting involves malicious scripts permanently saved on a server, such as in databases or comment fields. Every user visiting the affected page receives the payload automatically. This persistence makes it dangerous because it can compromise thousands of accounts silently.
DOM-Based XSS
This vulnerability exists entirely within the client-side code rather than on the server. The attack happens when the application uses JavaScript to process data from an untrusted source unsafely. The malicious script then modifies the Document Object Model environment directly.
Reflected vs. Stored vs. DOM: Quick Comparison
| Aspect | Reflected XSS | Stored XSS | DOM-based XSS |
|---|---|---|---|
| Where payload exists | In request (URL or input) | Stored in database/server | In browser DOM |
| Execution trigger | User clicks crafted link | User visits affected page | Client-side script execution |
| Persistence | Non-persistent | Persistent | Non-persistent (client-side) |
| Attack delivery | Requires user interaction | No interaction after injection | Triggered in browser logic |
| Visibility to server | Yes | Yes | No |
| Impact scope | Single user per attack | Multiple users affected | Depends on client-side usage |
Simulate attacker behavior and uncover advanced XSS payloads bypassing your defenses. Run a Pentest
Modern XSS Filter Bypass Techniques
Attackers do not rely on simple script injections anymore. Modern cross-site scripting bypass techniques are precise, layered, and built around exploiting the gaps between how filters read code and how browsers actually execute it.

1. Encoding and Obfuscation Techniques
Encoding is one of the oldest and most reliable bypass methods. Attackers transform payloads using URL encoding, HTML entities, Base64, or hex encoding to make them unrecognizable to pattern-based filters. The real trick is layering multiple encodings together. A filter that only decodes once will miss a payload encoded twice. The browser, however, keeps decoding until it finds something it can run.
2. Event Handler Injection
Filters typically block well-known event handlers like onclick and onerror. Attackers work around this by using obscure handlers that rarely appear on block lists. Handlers like onauxclick, onbeforetoggle, onscrollend, and onpointerrawupdate are valid in modern browsers but largely ignored by WAF rule sets. Injecting JavaScript through these handlers lets an attacker execute code without triggering a single filter rule.
3. DOM-Based XSS Bypass Techniques
DOM-based XSS bypass works by keeping the payload entirely on the client side. Since the server never processes the malicious input, server-side filters and WAFs have nothing to inspect. Attackers inject into DOM sinks like innerHTML, document.write, or location.href through URL fragments or client-side variables. Single-page applications built on React, Angular, or Vue are especially exposed to this because so much logic runs in the browser.
4. CSP Bypass Techniques
Content Security Policy is meant to stop unauthorized scripts from running. But a misconfigured CSP can be bypassed. Attackers look for whitelisted CDN domains that serve user-controlled content, use JSONP endpoints on trusted domains, or abuse strict-dynamic misconfigurations. If even one trusted source in the policy can be influenced by an attacker, the entire CSP protection collapses. A strong CSP needs nonce-based or hash-based policies to hold up reliably.
5. Polyglot XSS Payloads
A polyglot payload is crafted to execute across multiple injection contexts at once. It works inside HTML, JavaScript strings, URLs, and tag attributes without needing to be customized for each one. This makes it particularly effective during testing and real attacks because it covers several injection points with a single payload. Tools like Burp Suite use polyglots during scanning to quickly identify which contexts are vulnerable without needing to craft individual payloads per context.
6. Mutation XSS (mXSS)
Mutation cross-site scripting is one of the more subtle and dangerous bypass techniques. It works by injecting a payload that looks harmless when first parsed but mutates into executable JavaScript after the browser or a sanitization library processes it. DOMPurify, for instance, has had historical vulnerabilities where specific input combinations were sanitized safely but then re-mutated by the browser's HTML parser into something that executes. mXSS is hard to detect precisely because the payload does not look malicious at the point of inspection.
How Attackers Bypass Cross-Site Scripting Filters
Attackers bypass XSS filters by analyzing how input is processed and then crafting payloads that avoid detection using encoding, obfuscation, alternate execution paths, and browser parsing behavior.
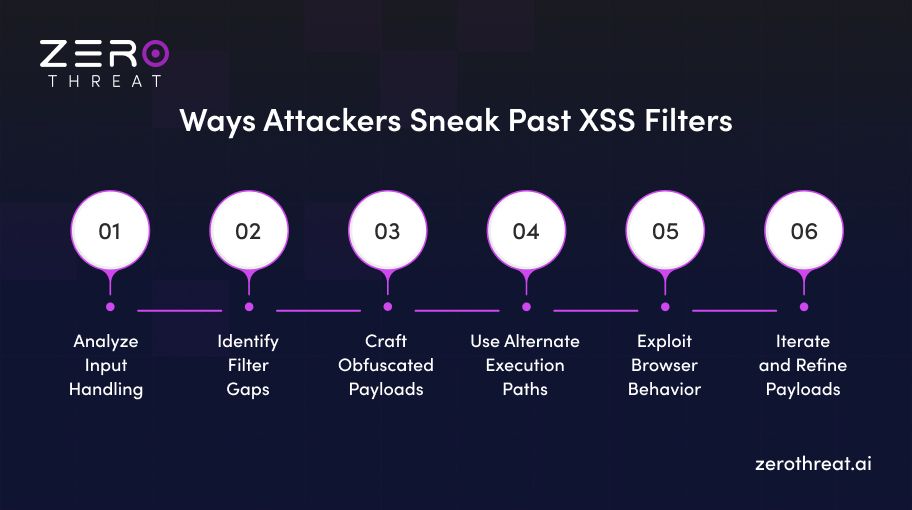
Step 1: Analyze Input Handling
Attackers first study how the application processes user input. They test different inputs across parameters, forms, and headers to understand filtering behavior. This helps them identify weak validation, incomplete sanitization, or inconsistent encoding across different parts of the application.
Step 2: Identify Filter Gaps
Once input behavior is clear, attackers look for gaps in filtering logic. Many filters rely on pattern matching and miss variations in syntax. Attackers test edge cases such as broken tags, mixed case keywords, or unusual input formats to find what bypasses detection.
Step 3: Craft Obfuscated Payloads
Attackers modify payloads using encoding, character splitting, or obfuscation techniques. This hides malicious intent from filters while still being understood by the browser. Techniques like nested encoding or invisible characters are commonly used to bypass signature-based detection.
Step 4: Use Alternate Execution Paths
Instead of relying on script tags, attackers use event handlers, JavaScript functions, or HTML attributes to execute code. These methods avoid traditional filtering rules and allow execution through browser-supported features that are often not fully restricted.
Step 5: Exploit Browser Behavior
Browsers automatically fix malformed HTML and decode encoded input. Attackers take advantage of this behavior by crafting payloads that appear harmless before rendering but become executable after parsing. This creates a gap between filter logic and actual execution.
Step 6: Iterate and Refine Payloads
Bypass is rarely achieved in one attempt. Attackers continuously test and refine payloads based on responses from the application. This iterative approach helps them adapt to defenses and eventually find a payload that executes successfully.
Continuous AI-powered pentesting at a price that fits your security budget. Check Out Pricing
Examples of XSS Filter Bypasses
Attackers use diverse encoding tricks to bypass filters that scan for specific suspicious strings. These examples demonstrate how attackers bypass signature-based detection by exploiting browser parsing flexibility and standards.
Character Encoding Tricks
Filters that scan for suspicious strings like javascript: can be defeated by encoding one or more characters in the payload. Attackers use HTML entity encoding, hexadecimal codes, Base64, or ASCII character codes to disguise the same string in multiple ways. What makes this particularly effective is that encodings can be nested, meaning the same payload can be encoded two or three times using different methods.
For example, replacing characters with their HTML entity equivalents or hiding a payload inside eval(atob(...)) with Base64 are both common, well-documented techniques that still find success against poorly configured input validation.
Whitespace Embedding
Browsers are very permissive with whitespace inside HTML and JavaScript. Attackers exploit this by embedding tabs, newlines, carriage returns, or other non-printing characters inside keywords to break up the strings that filters are scanning for. A filter looking for javascript: will miss it if the word is split with an encoded tab character in between.
The same applies to encoded newlines inserted at key positions in a URL attribute. While modern browsers have become stricter about some of these tricks, they still work in specific rendering contexts and older environments. For security teams, this is a reminder that filters need to normalize and strip whitespace before pattern matching, not after.
Tag Manipulation
When a filter simply scans input and removes a known bad tag like <script>, attackers nest the tag inside itself. After the filter strips out the inner match, the outer structure reassembles into a valid, executable script tag. Another common variation involves omitting spaces between tag attributes or using a forward slash as a separator, which many browsers accept as valid syntax but filters do not expect.
Case variation is also widely used here. Filters that block <script> in lowercase will often miss <SCRIPT>, <Script>, or mixed-case versions entirely. These tag manipulation techniques are simple but surprisingly effective against regex-based and pattern-matching filters.
How to Prevent XSS Attack Bypasses (Effective Strategies)
Preventing cross-site scripting bypass requires a layered security approach that focuses on secure data handling, strict browser controls, and safe coding practices. These strategies reduce attack surface and stop modern filter evasion techniques.

1. Use Context-Aware Output Encoding
Context-aware output encoding ensures user input is treated as data, not executable code. It converts special characters into safe formats before rendering in HTML, JavaScript, or URLs. This approach blocks script execution even if malicious input reaches the browser.
2. Implement Strict Content Security Policy (CSP)
A strong CSP header tells the browser exactly which script sources are trustworthy. This restricted environment prevents unauthorized scripts from running even if an injection occurs. It remains one of the most effective tools for mitigating modern cross site scripting vulnerabilities.
3. Validate and Sanitize Input Data
Input validation ensures only expected data formats are accepted, while sanitization removes unsafe content. This reduces the chances of malicious payloads entering the application. When combined with encoding, it creates a strong defense against injection attacks.
4. Use Secure Response Headers
Secure response headers add an extra layer of protection at the browser level. Headers like Content Security Policy, HTTPOnly cookies, and X-Content-Type-Options help control how content is interpreted. These controls reduce exposure to script execution and data theft risks.
5. Avoid Dangerous JavaScript APIs
Certain JavaScript APIs like eval, innerHTML, and document.write can execute untrusted input directly. Avoid using these functions with user-controlled data. Instead, use safer alternatives like textContent or secure DOM APIs to prevent unintended script execution.
How ZeroThreat Simplifies XSS Vulnerability Detection and Fixing
ZeroThreat simplifies XSS vulnerability detection by using AI-powered automated penetration testing that behaves like a real attacker. It discovers, exploits, and validates XSS flaws in real time, ensuring only exploitable issues are reported with clear remediation guidance.
Here is how ZeroThreat helps:
- Automatically crawls your web application and maps every input point that could be vulnerable to cross-site scripting injection.
- Tests each endpoint using advanced XSS payloads, including reflected, stored, and DOM-based attack vectors, to confirm real exploitability rather than just flagging theoretical risks.
- Detects filter bypass vulnerabilities by testing encoded payloads, event handler injections, and obfuscation techniques that traditional scanners miss entirely.
- Identifies DOM-based cross-site scripting in client-side JavaScript, including vulnerable sinks like innerHTML and document.write, which server-side tools cannot reach.
- Provides AI-powered remediation guidance for every finding, explaining the root cause, the injection context, and the exact fix required, whether that is output encoding, CSP configuration, or API replacement.
- Integrates into your development workflow so security testing happens continuously, not just before a release or audit.
- Generates detailed vulnerability reports that are useful for both developers fixing the issues and security teams tracking compliance and risk posture.
ZeroThreat reduces 90% of manual security effort with precise findings and clear remediation guidance that can accelerate fixes five times faster.
Talk to security experts about preventing advanced XSS bypass vulnerabilities faster.Contact Us
Conclusion: What to Do Next
Modern XSS attacks continue to bypass filters because attackers understand how browsers execute code better than most defenses. Filtering alone is not enough. You need to think beyond payload blocking and focus on how input is processed, rendered, and executed.
The most effective approach is layered security. Use context-aware encoding, enforce strict CSP, and avoid unsafe JavaScript practices. Regular testing is critical because cross-site scripting evolves with modern frameworks, APIs, and client-side logic.
ZeroThreat’s AI-powered automated pentesting simplifies by detecting vulnerabilities with 98.9 percent accuracy. Its agentic AI-driven exploit validation identifies real attack paths in web apps and APIs and provides you with remediation steps to fix XSS vulnerabilities in one go.
Frequently Asked Questions
How do modern XSS attacks bypass filters in real applications?
Modern cross-site scripting attacks bypass filters by exploiting how browsers parse and execute code differently from how filters inspect it. Attackers use encoding, malformed HTML, and alternate execution paths like event handlers, which filters often fail to detect.
What are the latest XSS payloads that work in 2026?
How do hackers bypass WAF protections using XSS?
What are common mistakes that allow XSS bypass?
How do modern frameworks still have XSS vulnerabilities?
How can I test XSS in a real web application?
What tools are best for finding XSS vulnerabilities?
Explore ZeroThreat
Automate security testing, save time, and avoid the pitfalls of manual work with ZeroThreat.


