
All Blogs
Out-of-Band Application Security Testing (OAST): Concept and Benefits

Quick Summary: Out-of-Band Application Security Testing (OAST) helps detect vulnerabilities that traditional testing methods often miss. This article explains the concept of OAST, how it works, the types of vulnerabilities it can uncover, and its key advantages. It also compares OAST with SAST and DAST, highlights common limitations, and provides practical insights for modern application security testing.
$15.63 trillion, this is the predicted cost of cybercrimes worldwide which is expected to become a reality by 2029, as per the report by Statista.
If this data seems concerning, think of 59 out of 100 organizations that have had a ransomware attack in the previous year. These statistics are indeed alarming!
It is enough to understand how significant the security of your software applications is today. Even a minute weakness can put your organization at risk. While you can adopt dozens of measures to protect the applications, security testing is critical to safeguard your web applications from the bottom.
Web application security testing is essential to identify weak spots in enterprise applications before they cause irreparable damage. While DAST (Dynamic Application Security Testing) is a solid technique to test and detect vulnerabilities, still a few goes undetected.
There comes the role of OAST techniques that empower the DAST model to catch other vulnerabilities. OAST helps to detect vulnerabilities that are not visible to the normal testing model.
Stay tuned to know what’s about OAST, how it benefits in testing applications, and what’s the best way to implement this in your application security testing strategy.
Let’s dig in for complete details!
Scan Your Application from Every Nook and Cranny to Protect from Data Breaches Try Now
Table of Contents
- What is Out-of-Band Application Security Testing?
- Common Vulnerabilities Detected by OAST
- What Does OAST Do That SAST and DAST Methods Can't?
- How Out-of-Band Application Security Testing Works
- What are the Advantages of OAST Testing?
- Limitations of Out-of-Band Application Security Testing
- SAST vs. DAST vs. OAST: Quick Comparison
- Final Thoughts
What is Out-of-Band Application Security Testing?
Out-of-band application security testing (OAST) is a method that uses external servers to detect invisible vulnerabilities. It works by forcing a target application to call back to infrastructure controlled by the tester. This approach reveals critical flaws that stay silent.
It originated as an evolution of Dynamic Application Security Testing (DAST) designed to detect vulnerabilities that do not return an immediate response, such as blind, asynchronous, or second-order vulnerabilities.
Common examples include Blind SQL injection and Server-Side Request Forgery. This technique ensures authoritative results by providing trusted confirmation whenever external systems are triggered.
Common Vulnerabilities Detected by OAST
By triggering external interactions, OAST uncovers critical flaws that DAST and SAST scanners often miss.
- Out-of-Band SQL Injection (OOB SQLi): Traditional testing fails when a database doesn't return errors. OAST forces the database to make an external DNS or HTTP request, confirming the vulnerability instantly.
- Blind Server-Side Request Forgery (SSRF): OAST detects Blind SSRF by forcing the server to reach out to a controlled listener. This confirms unauthorized access to internal resources when no response is visible.
- Blind Cross-Site Scripting (XSS): This identifies payloads that execute out of sight, such as in admin panels. OAST captures the "delayed" interaction, alerting you via an external callback without direct output.
- XML External Entity (XXE) Injection: OAST uncovers blind XXE by triggering the application's XML parser to reach out to an external server. This reveals sensitive data exfiltration or hidden server-side request flaws.
- OS Command Injection (OOB): When command injections return no output, OAST triggers an external interaction. This proves the system ran arbitrary code even if the application response remains completely silent.
What Does OAST Do That SAST and DAST Methods Can't?
OAST fills the critical vulnerability coverage gap left by SAST and DAST. Other methods rely on static code analysis or direct request-response cycles, while OAST uses external callbacks to confirm hidden security risks.
Detecting "Invisible" Vulnerabilities
SAST and DAST often miss bugs that do not trigger error messages, cause differences in application output, or create detectable time delays. OAST essentially sees "around corners" by monitoring for external interactions triggered by these silent flaws.
Eliminating Asynchronous Blind Spots
Traditional DAST struggles with asynchronous systems where an application processes a request in the background without sending an immediate response. OAST catches these vulnerabilities by waiting for the application to reach out to an external server whenever the flaw is finally triggered.
Providing High-Fidelity, Actionable Results
SAST often flags "potential" issues based on code patterns, which leads to high false-positive rates that waste developer time. In contrast, OAST confirms vulnerabilities through real network interactions; if the external server gets a hit, the vulnerability is almost certainly real.
Revealing Complex Zero-Day Threats
OAST can detect unusual responses or "canary" interactions that indicate zero-day vulnerabilities, such as the famous Log4Shell bug which was discovered via a DNS callback. This provides a level of proactive detection that traditional signature-based testing struggles to match.
Visibility in Distributed Architectures
OAST is highly effective at scanning modern microservices and APIs where data flows are often decoupled. It identifies security flaws in complex, multi-layered interactions that traditional "outside-in" dynamic testing simply cannot track.
Prevent potential security risks by pentesting your web application and APIs. Find Security Issues
How Out-of-Band Application Security Testing Works
Out-of-band Application Security Testing works by triggering external network interactions from the target application. Instead of analyzing immediate responses, it confirms vulnerabilities by monitoring DNS, HTTP, or other callbacks generated when the application processes a malicious payload.
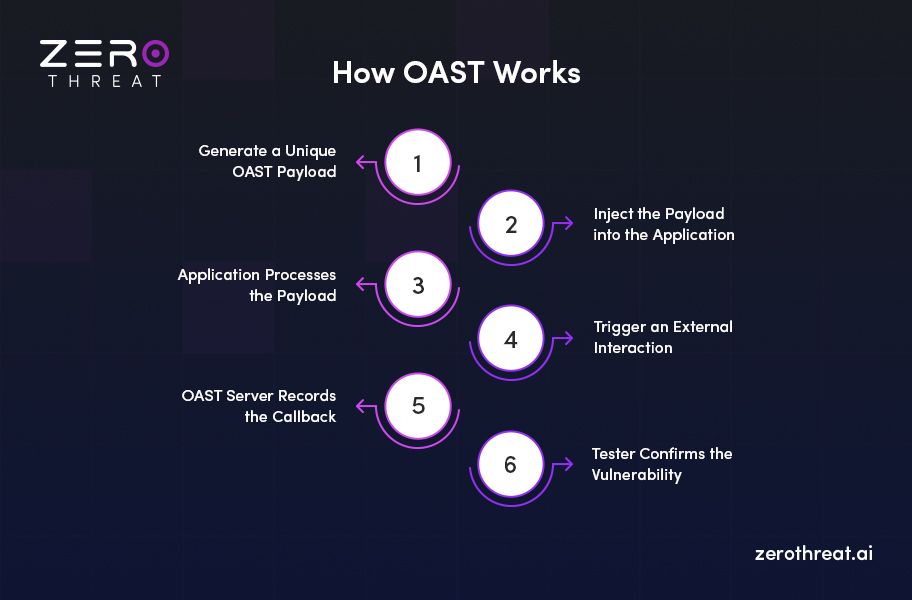
Step 1: Generate a Unique OAST Payload
The testing process begins by creating a payload that includes a unique external domain controlled by the tester or a security testing tool. This domain acts as the interaction point for detecting outbound requests.
Step 2: Inject the Payload into the Application
The payload is then injected into different input points in the application. These may include form fields, API parameters, headers, file uploads, or other user-controlled inputs where vulnerabilities might exist.
Step 3: Application Processes the Payload
If the application is vulnerable, it processes the injected payload during backend operations. This may happen through database queries, XML injection, system commands, or server-side requests.
Step 4: Trigger an External Interaction
When the payload executes, the application may attempt to connect to the external domain embedded in the payload. It usually occurs through DNS lookups, HTTP requests, or other outbound network calls.
Step 5: OAST Server Records the Callback
The external OAST server logs the incoming interaction from the application. These logs capture details such as the request type, timestamp, source IP, and protocol used.
Step 6: Tester Confirms the Vulnerability
Security testers analyze the recorded interaction to verify that the application executed the payload. This confirms the presence of vulnerabilities such as SSRF, blind SQL injection, XXE, or command injection.
What are the Advantages of OAST Testing?
OAST testing provides realistic results and offers many advantages, as mentioned below.
- Increased Coverage: OAST testing can detect more security issues since it can find vulnerabilities that dynamic testing detects. This higher scope of vulnerability detection makes it more effective in application security testing. It is depicted in the image below.
- Improved Testing Results: Most vulnerabilities captured with out-of-band testing are real compared to dynamic and static testing methods. Hence, it results in more accurate testing results.
- False Positives are Rare: While dynamic testing can provide a few false positives, out-of-band application security testing rarely produces any false positives.
- Language Agnostic: OAST testing does not depend on any specific programming language. So, it is possible to test many different types of applications irrespective of which language they use.
- Easy Integration: Integrating the OAST testing tool with your application development workflow is easy and offers quality testing.

Limitations of Out-of-Band Application Security Testing
While OAST is a powerful way to find hidden bugs, it isn't a perfect security testing method, just like SAST and DAST. Understanding its boundaries helps you build a more realistic and effective security strategy.
- Dependency on External Infrastructure: OAST relies entirely on an external server to receive callbacks. If this listener is offline or its IP is blocked, you will miss critical vulnerabilities.
- Gaps in Complex Environments: Highly segmented or strictly isolated networks can block the outbound traffic OAST needs. This limited visibility can prevent the detection of vulnerabilities in restricted zones.
- Manual Testing is Still Essential: Automated tools lack human intuition. Complex logic flaws and deep architectural risks often require a skilled pentester, as OAST cannot replace expert manual review.
- Challenges with Specific Exploits: In certain configurations, OAST may struggle to detect complex SSRF or XXE vulnerabilities. These scenarios often require advanced manual tuning or specialized testing tools for confirmation.
- No Direct Code-Level Visibility: Since OAST tests from the outside, it cannot pinpoint the exact line of code causing the issue. Developers must still search the codebase manually to fix it.
SAST vs. DAST vs. OAST: Quick Comparison
| Feature | SAST (Static) | DAST (Dynamic) | OAST (Out-of-Band) |
|---|---|---|---|
| Testing Approach | White-Box: Analyzes source code without running it. | Black-Box: Tests the running application from the outside. | Callback-Based: Uses external servers to find "invisible" flaws. |
| When it’s Used | Early in the development cycle (coding phase). | During runtime or in a staging environment. | During runtime to catch asynchronous or blind bugs. |
| Accuracy | Low: Often produces many false positives. | High: Results are usually real but can miss hidden bugs. | Very High: If a callback is received, the bug is almost certainly real. |
| Visibility | Full visibility into the underlying code. | Simulates a real-world attack surface. | Sees invisible interactions outside the direct response. |
| Blind Bug Detection | No; it cannot predict complex runtime interactions. | Limited; misses bugs that don't send an immediate response. | Excellent; specifically designed for blind SQLi, XSS, and SSRF. |
Need help detecting hidden vulnerabilities in your application? Contact Us
Final Thoughts on Out-of-Band Application Security Testing
With the increasing incidents of cybercrimes, it becomes more important than ever to boost your application’s security. Besides implementing solid features, security testing is crucial to find vulnerabilities and fix them before they pose any serious security challenges. OAST is a dynamic application security testing method that offers numerous advantages over other testing methods.
Choosing the right OAST tool is vital for detecting OOB vulnerabilities, and ZeroThreat is the one that you can rely on. Its automated pentesting tool detects out-of-band vulnerabilities with a bunch of great features to meet your organizational expectations. You can leverage this to discover hard-to-detect vulnerabilities with OAST security audits. This tool uses AI to enhance test results and help testers achieve their objectives seamlessly.
Frequently Asked Questions
What is the main goal of using OAST?
Out-of-band OAST is designed to detect "invisible" vulnerabilities that do not trigger error messages or immediate responses. By using an external server to monitor for interactions, it uncovers blind flaws like SQLi or SSRF that traditional dynamic testing methods often miss.
How do I automate this process in my security pipeline?
Is OAST effective for modern microservices and APIs?
Which methods are typically used to trigger external interactions?
Explore ZeroThreat
Automate security testing, save time, and avoid the pitfalls of manual work with ZeroThreat.


