All Blogs
API Authentication vs API Authorization: The API Security Gaps Developers Overlook
Quick Overview: Modern applications rely on APIs for critical communication, making secure identity and access controls essential. In this blog, we explore the difference between authentication and authorization, examine common failure patterns, and highlight practical strategies to prevent issues like BOLA, weak tokens, and authorization drift.
Modern applications rely on APIs for everything—from web app connectivity to microservices communication and third-party integrations. As organizations adopt more distributed architectures, API exposure increases, and with it, the complexity of securing identity and access layers.
Two concepts sit at the heart of API security: authentication (authN) and authorization (authZ). They are often mentioned together, sometimes confused, and frequently misimplemented. While authentication determines who a client or user is, authorization determines what they can do.
Both are essential. Both can fail in subtle and dangerous ways.
This article explores the key differences between authentication and authorization, the most common failure patterns observed in real-world APIs, and how security engineers and teams can prevent them. The goal is to provide a clear, actionable understanding for both technical implementers and security decision-makers.
Secure your APIs with automated testing—start instantly. Get Started Now
On This Page
- What is API Authentication?
- Common API Authentication Methods
- What is API Authorization?
- Authorization Models: RBAC, ABAC, and OAuth Scopes
- Common Authentication Failure Patterns
- Common Authorization Failure Patterns
- Difference Between Authentication and Authorization
- How Do Authentication and Authorization Work Together?
- API Authentication vs API Authorization: Comparison Table
- Best Practices to Prevent API Authentication and API Authorization Issues
- Adopt a Next-Gen API Security Tool – ZeroThreat
- Final Thoughts
What is API Authentication?
API authentication is a security process that verifies the identity of a user or application attempting to access an API. Its primary purpose is to ensure that only authorized entities can interact with the API and its resources, which prevents unauthorized access, data breaches, and misuse. By confirming who is making the request, authentication helps protect sensitive information and resources from unauthorized access.
Modern APIs rely on secure standards like OAuth 2.0, JWTs, API keys, mTLS, and token-based workflows to maintain trust between distributed services. Beyond simply checking credentials, robust API authentication should handle token rotation, session expiry, multi-factor validation, and protection against common threats such as token replay or credential stuffing.
When implemented correctly, it provides a secure, scalable, and seamless way to control who can interact with your APIs—laying the foundation for a stronger overall security posture.
Common API Authentication Methods
Modern APIs rely on several well-established authentication mechanisms to verify the identity of users, applications, and services before granting access. These methods range from simple approaches like API keys, used for basic identification, to more advanced standards such as OAuth 2.0 and JWTs, which support delegated access, token-based workflows, and granular permission controls.
Moreover, some deployments use mutual TLS (mTLS) for strong, certificate-based validation between machines, while others adopt HMAC signatures to ensure request integrity. Each method serves a specific purpose, and choosing the right one depends on security requirements, scalability needs, and the sensitivity of exposed data.
What is API Authorization?
API authorization defines what an authenticated user or system is allowed to access or perform within an API. It follows API authentication, which verifies the identity of the user or system. It enforces access control policies that prevent users from viewing, modifying, or interacting with resources they shouldn’t have access to.
Effective authorization validates roles, permissions, object ownership, and multi-step workflows to ensure every request aligns with defined security rules. This includes safeguarding against critical issues like BOLA (Broken Object Level Authorization), BFLA (Broken Function Level Authorization), and privilege escalation—some of the most common and damaging API vulnerabilities today.
API authorization determines what an authenticated user or application is allowed to do. Once your identity is confirmed through authentication, authorization steps in to manage permissions, ensuring that users can only access resources that align with their roles and privileges.
In an API context, this involves defining specific permissions for different users or applications. For instance, one user might have read-only access to certain data, while another can edit it. With the rise of zero-trust security principles, it's increasingly important to evaluate authorization at every API call, reinforcing the need for precise control over who can do what in your digital ecosystem.
Authorization Models: RBAC, ABAC, and OAuth Scopes
Modern APIs rely on structured authorization models to enforce fine-grained access control and ensure users only perform actions within their intended privileges.
Role-Based Access Control (RBAC) assigns permissions based on predefined roles such as admin, user, or auditor, making it simple and scalable for most applications.
Attribute-Based Access Control (ABAC) adds deeper context by evaluating attributes, like user identity, resource type, request time, or environment, to make dynamic, policy-driven decisions.
OAuth scopes provide another layer of precision by limiting what third-party applications or tokens can access, defining boundaries such as “read-only,” “write,” or “admin-level” privileges.
Together, these models help organizations align API access with security requirements, minimize over-privilege, and reduce the risk of unauthorized actions across distributed systems.
Common Authentication Failure Patterns
Below are the most common authentication failure patterns organizations face, and how these weaknesses are typically exploited in real-world attack scenarios.
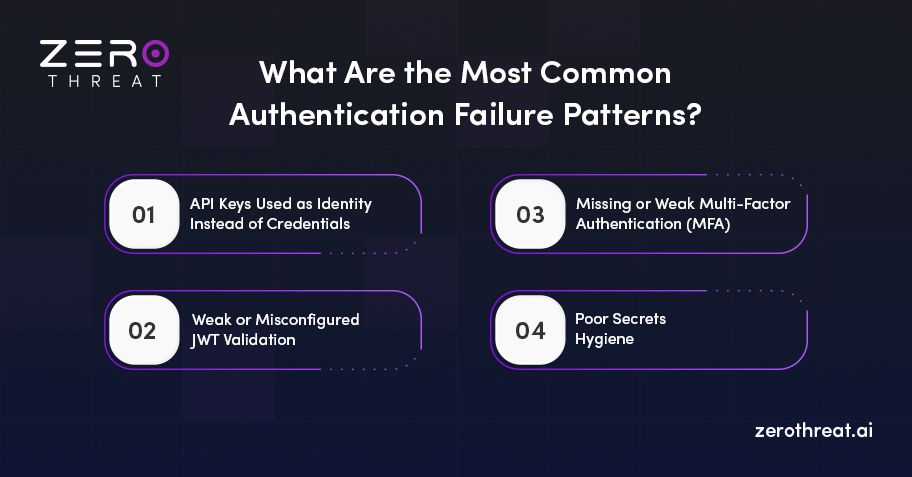
1) API Keys Used as Identity Instead of Credentials
API keys are attractive because they're simple. But they often become a replacement for proper identity mechanisms.
Failure symptoms:
- Same API key used by multiple services or environments
- Keys embedded in mobile apps or JavaScript
- No rotation or expiration
- Over-scoped permissions tied to a static secret
Why it fails:
API keys are bearer secrets, anyone who has them gains access. They don’t prove identity or support granular authorization.
Mitigations:
- Treat API keys as session credentials, not identity
- Use OAuth 2.0 or signed tokens for user/service identity
- Implement rotation, scoping, and short TTLs
2) Weak or Misconfigured JWT Validation
JWTs are powerful but easy to misuse. Common mistakes include:
- Accepting unsigned or weakly signed tokens
- Not validating token issuer, audience, or expiration
- Using “none” algorithm vulnerabilities
- Failing to check token revocation
Why it fails:
JWTs enable stateless auth, but their security depends entirely on correct signature verification and claim validation.
Mitigations:
- Validate iat, exp, iss, aud, and sub claims
- Rotate signing keys using JWKS endpoints
- Enforce strict signature verification
- Avoid embedding sensitive data
3) Missing or Weak Multi-Factor Authentication (MFA)
Especially in administrative APIs, lack of MFA dramatically increases breach risk.
Typical issues:
- MFA only on UI, not API endpoints
- Bypassable MFA flows
- Tokens issued prior to MFA revalidated indefinitely
Mitigations:
- Require MFA for privileged API operations
- Use step-up authentication for sensitive transactions
4) Poor Secrets Hygiene
Developers accidentally leak secrets everywhere: GitHub, logs, build artifacts, mobile binaries.
Failure symptoms:
- Hardcoded secrets
- Lack of environment segregation
- No secret rotation plan
Mitigations:
- Use centralized secret managers
- Scan repos and pipelines for leaked credentials
- Automate rotation and revocation
Find real API vulnerabilities with next-gen automated pentesting. Run an API Pentest
Common Authorization Failure Patterns
Authorization failures are more subtle and often far more damaging. They frequently map to the OWASP API Top 10 categories such as BOLA/Broken Object Level Authorization, BFLA, and excessive data exposure.

1) Broken Object Level Authorization (BOLA)
(Also known as IDOR—Insecure Direct Object Reference.)
This is the most common and impactful API vulnerability.
What happens:
A user changes an object ID in a request and accesses another user’s data:
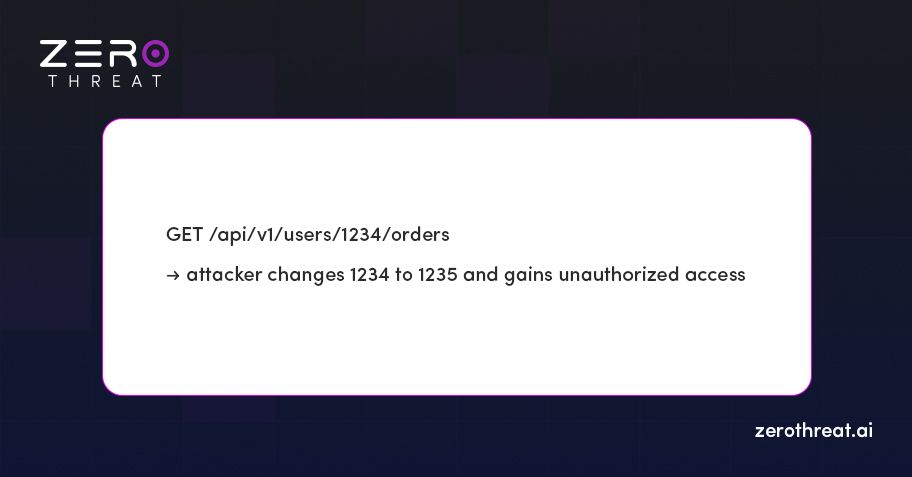
Failure cause:
Authentication succeeded, but authorization did not enforce resource ownership.
Mitigations:
- Enforce object-level access checks on every request
- Never rely solely on user-provided IDs
- Use internal surrogate identifiers
2) Broken Function Level Authorization (BFLA)
Authorization must not only control resource access but also available operations.
Example:
A regular user discovers an admin-only endpoint like:
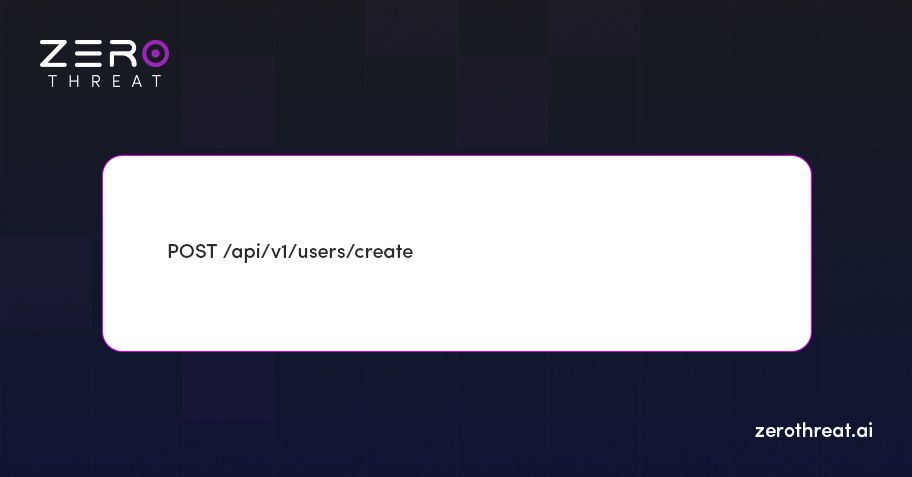
Why it fails:
Functionality-level permissions are not checked or rely solely on UI restrictions.
Mitigations:
- Implement server-side RBAC/ABAC checks
- Maintain least privilege
- Avoid relying on client-side discovery
3) Overly Broad Scopes in OAuth and API Tokens
OAuth providers often grant far more access than intended.
Common issues:
- Mobile apps requesting full account scope
- Machine-to-machine tokens granting wildcard access
- Refresh tokens with long-lived, unrestricted privileges
Mitigations:
- Use granular scopes aligned with API endpoints
- Limit refresh token lifespan
- Separate user vs machine scopes
4) Improper Multi-Tenancy Isolation
Multi-tenancy introduces complex access-control boundaries.
Failure symptoms:
- Tenant A accessing tenant B’s resources
- Cross-tenant enumeration
- Missing tenant context in backend authorization checks
Why it fails:
Authorization logic is applied at the wrong layer or inconsistently across microservices.
Mitigations:
- Enforce tenant checks at gateway and service layers
- Use isolation keys (tenant_id) as part of every query
- Test for cross-tenant leakage during CI security scanning
5) Hidden or Shadow Endpoints Without Authorization
Internal or deprecated API endpoints often lack proper authorization because they were never intended for public access.
Examples:
- Debug endpoints
- Legacy versions (e.g., /v1/internal/*)
- Uncatalogued microservice routes
Mitigations:
- Maintain API inventories via automated discovery
- Enforce authentication and authorization globally
- Route all endpoints through the same enforcement layer
Difference Between Authentication and Authorization
Authentication and authorization are two foundational pillars of API security, but they serve very different purposes. Understanding this distinction is essential for designing secure APIs and preventing common vulnerabilities.
Authentication: Proving Identity
Authentication answers a simple question: Who are you?
It verifies the identity of the user, application, or service making the request before granting access to any protected API route.
Key points:
- Confirms identity using credentials such as API keys, OAuth tokens, JWTs, passwords, or certificates.
- Ensures the requester is legitimate and not an unknown or spoofed entity.
- Always happens before authorization.
Authorization: Defining Permissions
Authorization answers the next question: What are you allowed to do?
Once the identity is confirmed, authorization determines which actions, resources, or data the authenticated entity can access.
Key points:
- Enforces permissions, roles, scopes, and access policies.
- Prevents users from performing actions outside their intended privilege level.
- Protects against issues like BOLA, privilege escalation, and unauthorized data access.
Flexible plans designed for every security team. View Pricing
How Do Authentication and Authorization Work Together?
While authentication and authorization are different, they work in a strict sequence:
- Authentication verifies identity.
- Authorization determines permissions based on that identity.
You can think of it like entering a building:
- Authentication checks your ID at the front door.
- Authorization decides which rooms inside the building you’re allowed to enter.
Why the Distinction Matters
While talking about authentication vs authorization in API, mixing the two or treating them interchangeably leads to serious security gaps, such as:
- Authenticated users accessing sensitive records (missing authorization).
- Public endpoints exposed without identity checks (missing authentication).
Clear separation of these controls helps ensure that APIs remain secure, predictable, and resilient against modern attack techniques.
API Authentication vs API Authorization: Comparison Table
| Aspect | Authentication | Authorization |
|---|---|---|
| Purpose | Verifies who the user or system is | Determines what the user or system can do |
| Primary Question | “Who are you?” | “What are you allowed to access?” |
| Function | Confirms identity using credentials | Enforces permissions, roles, and access policies |
| When It Happens | Always occurs first, before access is granted | Occurs after authentication is successful |
| Controls Involved | Passwords, API keys, OAuth tokens, JWTs, mTLS certificates | RBAC, ABAC, OAuth scopes, ACLs, policy engines |
| Prevents | Unauthorized or anonymous access | Privilege escalation, BOLA, data exposure |
| Outcome | Grants access to the system | Grants or denies access to specific resources/actions |
| Visibility | Often visible to users (login screens, tokens) | Usually happens in the background (permission checks) |
| Example | Sign in to verify your identity | Access allowed only to your own records, not others' |
Best Practices to Prevent API Authentication and API Authorization Issues
Securing your APIs requires more than just implementing login mechanisms or basic role checks. Modern threats often exploit gaps in API authentication vs authorization, including weak credential handling, inconsistent access controls, and flaws in business logic.
By following proven best practices, organizations can significantly reduce risk, protect sensitive data, and maintain trust across their applications and user base.
1) Enforce Strong, Token-Based Authentication
Use modern standards such as OAuth 2.0, OpenID Connect, and JWTs to authenticate users and services. These approaches clarify authorization vs authentication in API design, offering stronger security, better scalability, and improved lifecycle management compared to static API keys or passwords.
Why it matters:
Strong authentication reduces impersonation risks and supports secure integrations with external systems.
2) Apply Least Privilege Through Granular Authorization
Limit each user or service to only the minimum level of access required. Use RBAC, ABAC, or OAuth scopes to enforce structured, precise permission models.
Why it matters:
Granular authorization prevents privilege escalation and restricts the blast radius of potential breaches.
3) Validate Object Ownership Consistently
Always confirm that users can access only the data they own. Clear enforcement of API authorization vs authentication is essential to prevent BOLA (Broken Object Level Authorization), the most common and severe API vulnerability.
Why it matters:
Proper ownership checks protect customer data and avoid regulatory exposure.
4) Protect Endpoints with Strong Session & Token Controls
Implement short-lived access tokens, automatic rotation, refresh token boundaries, and strict expiration rules. Use mTLS for service-to-service authentication where appropriate.
Why it matters:
Reduces token theft, replay attacks, and long-lived credential compromise.
5) Centralize Authorization Logic
Avoid scattering authorization checks across multiple services. Instead, use middleware, API gateways, or policy engines (OPA, AWS IAM, etc.) to enforce consistent rules.
Why it matters:
Centralization lowers implementation errors and simplifies audits.
6) Monitor Authentication Flows for Anomalies
Track failed login attempts, suspicious access requests, brute-force patterns, and token misuse. Integrate logs with SIEM tools for real-time detection.
Why it matters:
Early detection of anomalies reduces both financial and reputational damage.
7) Continuously Test Authentication & Authorization
Use automated pentesting platform, threat modeling, and regular access reviews to identify gaps early. Testing business logic flows—especially authentication vs authorization in API—is critical, not just individual endpoints.
Why it matters:
Proactive testing reduces breach likelihood and ensures security keeps pace with product changes.
Need help or guidance? Our team is here for you. Talk to Us
Adopt a Next-Gen API Security Tool – ZeroThreat
Modern API ecosystems require more than traditional scanners or static rulesets. ZeroThreat delivers continuous, intelligent, and context-aware security that closes the gaps where authentication and authorization failures typically occur.
Designed for security engineers and decision-makers, ZeroThreat provides full visibility into your API attack surface and real-time detection of the vulnerabilities that matter most.
By adopting ZeroThreat, organizations gain a proactive layer of defense that evolves with their API architecture. Whether you're managing microservices, public APIs, or large-scale distributed applications, ZeroThreat ensures authentication and authorization controls stay reliable, consistent, and attack-resistant. It's not just a scanner; it’s a purpose-built API security intelligence platform that helps teams detect failures before attackers do.
If you wish to secure your APIs, try ZeroThreat now for just $25.
Final Thoughts
API Authentication and API authorization are the foundation of API security, yet they remain two of the most commonly misunderstood and misimplemented controls in modern application development.
Breaches caused by BOLA, excessive permissions, weak token validation, and poor identity management demonstrate that getting authN and authZ right is not optional, but it’s essential.
By recognizing the failure patterns outlined in this article and implementing structured, defense-in-depth strategies, organizations can significantly reduce risk across their API ecosystem.
Frequently Asked Questions
What is the difference between API authentication and authorization?
While talking about the difference between API authentication and authorization, authentication verifies who a user or service is, while authorization determines what they can access or do. Authentication proves identity using credentials or tokens; authorization enforces permissions, roles, and resource-level rules. Both are essential, but they serve different purposes and must work together to keep APIs secure.
Why do APIs often fail to separate authentication from authorization correctly?
What are the most common authentication failure patterns in APIs?
How can developers prevent IDOR and other object-level authorization issues?
Can JWTs introduce security risks if not implemented properly?
How can API gateways help reduce authentication and authorization failures?
Explore ZeroThreat
Automate security testing, save time, and avoid the pitfalls of manual work with ZeroThreat.


